Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
ManageEngine EventLog Analyzer Review

UPDATED: October 8, 2021
syslog Event Log Analyzer from ManageEngine is one of the preferred SIEM log management software of cyber-security consultants and white-hat hackers.
It can keep all event logs and Syslogs in one place, sort them out, and analyze them in real time. It is a no brainer when it comes to your security logs.
What are Event Logs, and how can we Manage them?
Event logs from Windows workstations, servers, domain controllers, and Syslog‘s from Unix systems or networking devices save records of events for security, application, directory service, and more. Such events can happen within an organization network systems.
System Log management, which involves event log management and Syslog management, is a key component in almost all enterprises.
Such a system is capable of identifying security incidents, fraudulent activity, policy violations, and operational issues.
A Log Management Solution
Many organizations underestimate the need for a complete log management solution.
Without it, network admins would spend long hours sifting through hundreds of log messages to Pinpoint and troubleshoot a problem. Efficient log analysis can increase network performance, reduce system downtime, and can even help tighten security policies within the organization.
But that is not all; a log management solution can also help in regulatory compliance, including GLBA, HIPAA, PCI, and Sarbanes-Oxley (SOX). Such regulations may require archiving logs and providing reports for specific security audits.
In this in-depth product Review of ManageEngine EventLog Analyzer, we will take a closer look at one of the most popular Event Log analyzers in the Market and go in-depth into its capabilities.
- What is EventLog Analyzer?
- How Does EventLog Analyzer Work?
- Security Information Management.
- Windows Event Log Management.
- Syslog Management.
- Application Logs Management
- Regulatory Compliance Audits & Reports
- GLBA Compliance Reports
- HIPAA Compliance Reports
- PCI Compliance Reports
- SOX Compliance Reports
- Log Management Features
- Log Collection
- Log Analysis
- Log Archiving
- Importing Event Logs
Lets Review ManageEngine EventLog Analyzer
EventLog Analyzer from ManageEngine is an agentless web-based event and application log monitoring and management tool.
It is capable of collecting, analyzing, and archiving in real-time, event logs from distributed Windows hosts and Syslogs from distributed Unix hosts, or network devices.
EventLog Analyzer can also collect application logs from IIS FTP server, IIS Windows web server, Oracle database server, MS SQL server, DHCP Windows and Linux servers.
How Does EventLog Analyzer Work?
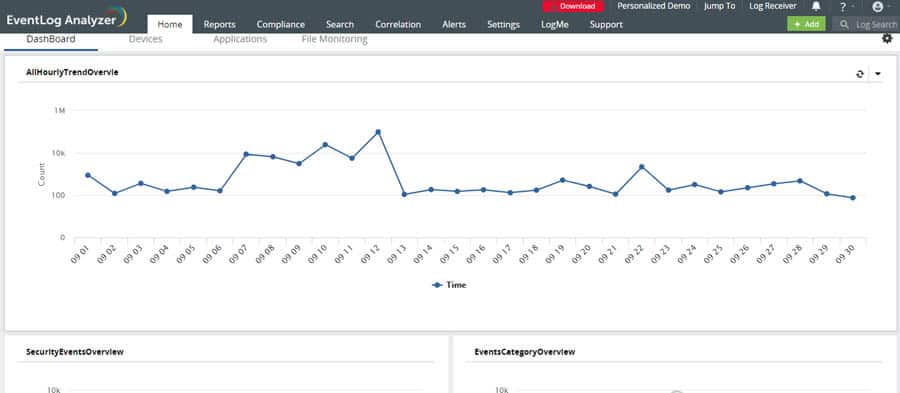
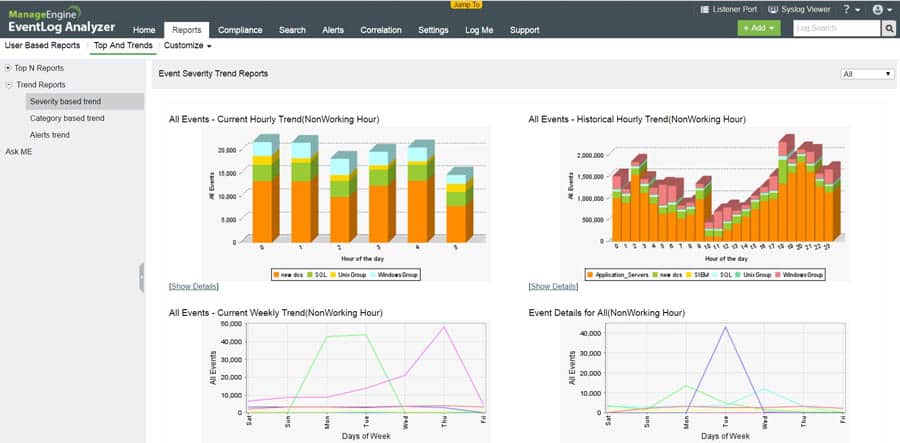
The EventLog Analyzer collects, analyzes, searches, correlates, reports, and stores logs from a centralized platform.
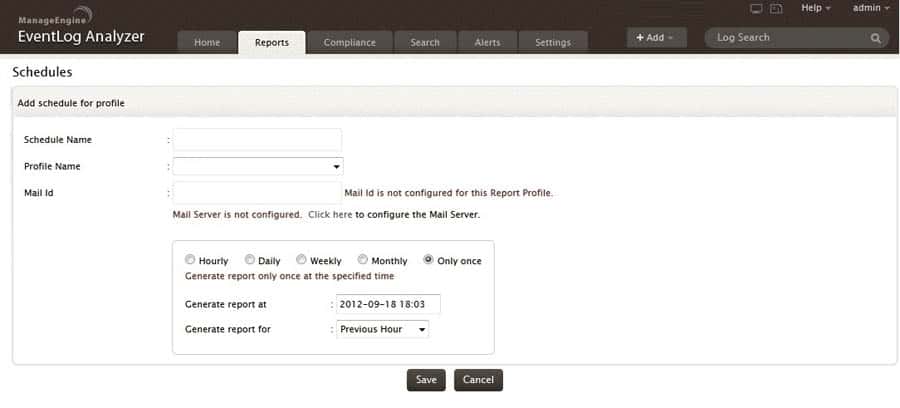
It then converts that data into easy to understand reports and graphs. In case that any abnormal behavior is detected, the software sends security alerts in real-time via email or SMS.
Notable Features
EventLog Analyzer has several features that are worth noting:
- Event log management
- Syslog management
- Application log monitoring
- Security Information and Event Management
- Server Log Management
- Oracle and SQL Database Auditing
- Real-time Event Correlation
- Real-time Event Alerts
- Network Monitoring
- IT Compliance Reporting
- Event log monitoring
- Security Log Monitoring
- GDPR compliance reports
Security Information Management
Windows Event Log Management
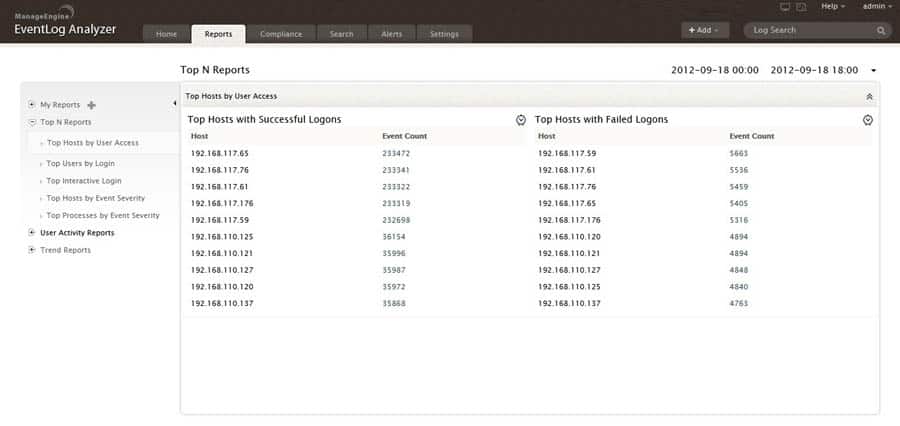
Windows Event Log Monitor and Analysis are the two essential functions performed for Windows Event Log Management. As part of the monitoring, the tool collects, normalizes, and aggregates Windows Event Logs.
The Windows Event Log Analyzer application examines the logs and generates pre-built reports, regulatory compliance reports, or historical trend reports. It can also create alerts for anomalous and specific Windows log events.
The Windows Event logs need to be archived for network auditing and more recently to comply with various regulations such as GLBA Compliance, HIPAA Compliance, PCI-DSS Compliance, and the Sarbanes-Oxley (SOX or SARBOX).
Apart from this, system administrators look at event logs as a critical source for troubleshooting performance problems on hosts across the entire network.
EventLog Analyzer also supports logs received from other Syslog supported systems and devices.
Windows Event Log monitoring is a prime function of the EventLog Analyzer. It supports the Windows logs of all versions, such as Windows 2000, 2003, and Windows XP.
The event log manager software can also analyze the Windows Vista event logs, which is in extended EVT format.
Syslog Management
System log (Syslog) management is a security requirement in almost all enterprises. System administrators look at Syslog as a critical source to troubleshoot performance problems on Syslog supported systems and devices across the network.
The EventLog Analyzer functions like a Syslog daemon or a Syslog server and collects the events by listening to the Syslog port (UDP). The Event log analyzer can examine, report, and archive the Syslog events (including Syslog-ng) received from all the Syslog-supported systems and devices.
The tool also manages the events of systems supporting Unix, Linux, Solaris, HP-UX, IBM-AIX Syslogs and devices supporting Syslog like routers, switches (Cisco) or any other device.
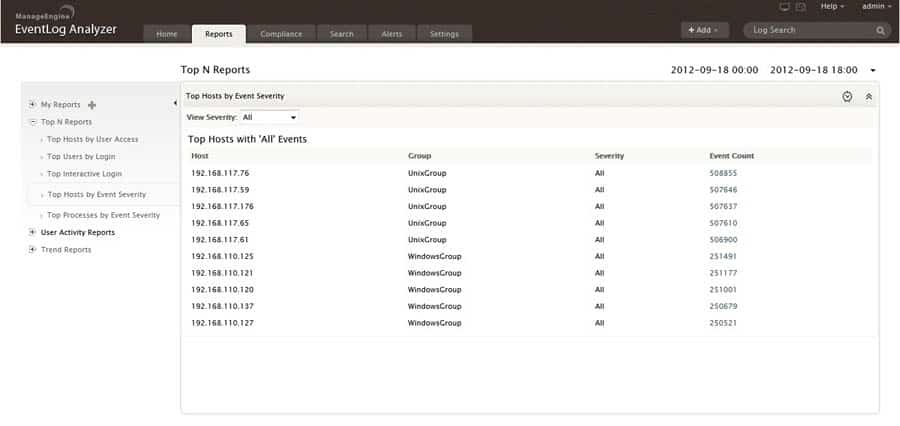
Using the EventLog Analyzer, you can generate Syslog reports in real-time, and then archive these Syslogs.
You get instant access to a wide variety of reports for Syslog events generated across hosts, users, processes, and host groups.
Application Logs Management
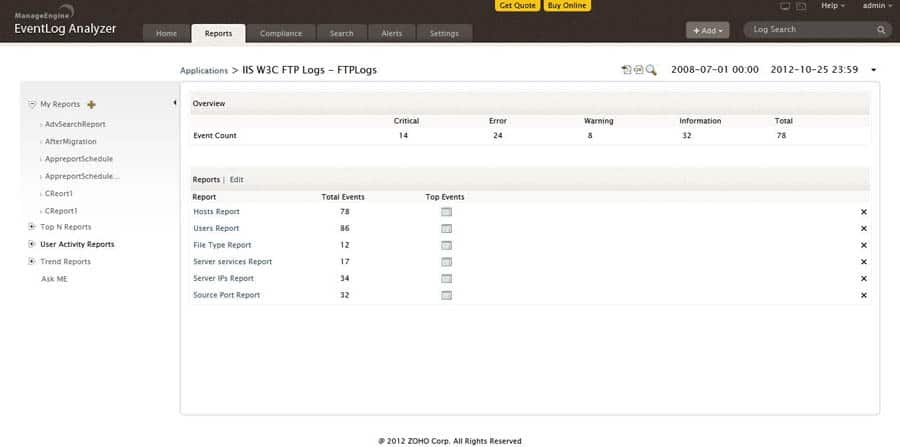
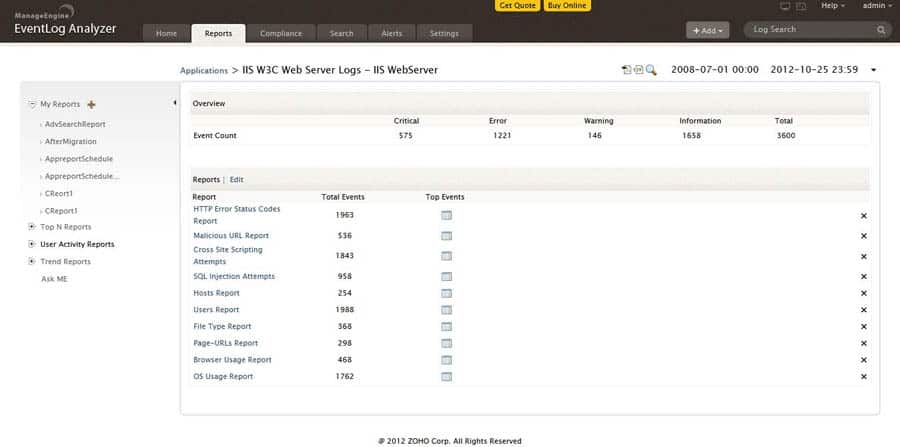
The EventLog Analyzer includes value-added application logs analysis reports. The server applications like web-server, FTP server, and SQL application “MSSQL logs,” are analyzed and reported.
The server applications logs supported are IIS W3C Web Server logs and IIS W3C FTP Server logs.
The SQL application logs supported is MSSQL Server logs. These reports show you the details of the top events generated, event trends, and more.
Using these reports, administrators can quickly determine errant users and abnormal behavior of applications, thereby reducing the troubleshooting cycle.
The IIS W3C Web Server logs provide details of clients, users, file types wise access, page URL-wise access, browser-wise usage, and OS wise-usage. It also offers a Malicious URL report and HTTP Error Status Codes report.
The IIS W3C FTP Server logs reports provide details of clients and users. It includes file transfer details and file types, server, services, server IPs, and source ports reports.
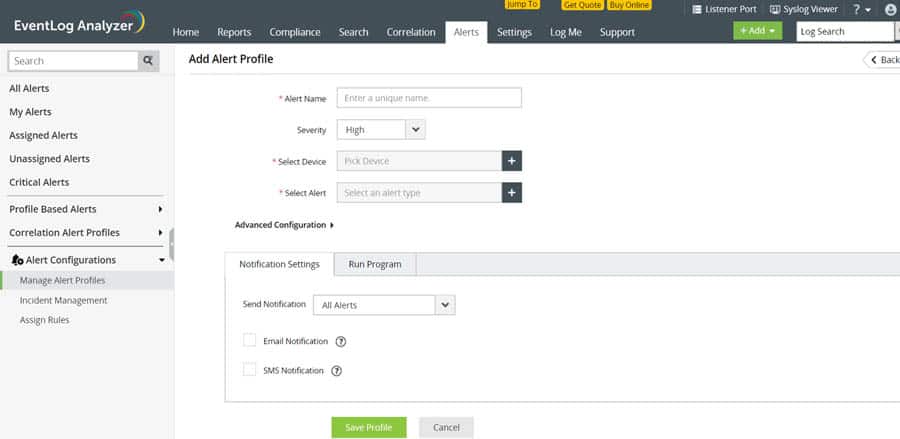
Alerts and Notifications
The EventLog Analyzer includes alerts on event logs which notify administrators when an event matching specific criteria is generated. Alerting helps administrators monitor critical servers and processes on the network without spending too much time watching graphs and reports.
With this tool, you can define which hosts or group of hosts need to be monitored. Depending on the size of your organization, critical processes may run on a single dedicated server, or be spread out over a group of servers.
The EventLog Analyzer lets you set up alerts for events generated in both cases. If you need to trigger an alarm based on events with a specific log type, log message, or severity, you can define a custom alert profile to notify administrators.
The EventLog Analyzer includes a list of predefined event status messages for Windows and UNIX hosts. You can set an alert by choosing a status message from this list. Typical status messages include:
- Failed login
- Audit logs cleared
- DNS shutdown
- and more.
If you need to trigger an alert based on a specific type of compliance violation for GLBA, HIPAA, PCI, or SOX, based on failed login attempts, policy changes, account changes, and audit logs cleared, you can define a compliance alert profile to notify administrators.
You can also set up the EventLog Analyzer to notify operators by email whenever an alert is triggered. Instant email notifications help IT identify problems faster and focus on solving them.
Regulatory Compliance Audits & Reports
EventLog Analyzer provides exclusive reports to help comply with various regulatory acts such as:
- GLBA – Gramm-Leach-Bliley Act
- HIPAA – Health Insurance Portability And Accountability Act
- PCI DSS – Payment Card Industry Data Security Standard
- Sarbanes-Oxley Act
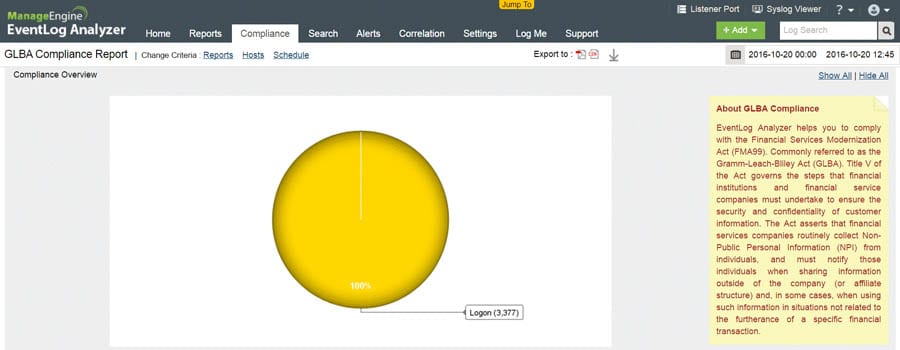
GLBA Compliance Reports
The Section 501 of the Gramm-Leach-Bliley Act (GLBA) documents specific regulations required for financial institutions to protect “non-public personal information.”
As part of the GLBA requirements, it is necessary that a security management process exists to protect against attempted or successful unauthorized access, use, disclosure, modification, or interference of customer records.
In other words, being able to monitor, report, and alert on attempted or successful access to systems and applications that contain sensitive customer information.
The EventLog Analyzer meets the system monitoring and reporting requirements of GLBA Regulations.
With EventLog Analyzer, you can easily monitor your network systems for any insider activity. GLBA regulations mandate analysis of all logs, including OS and application logs.
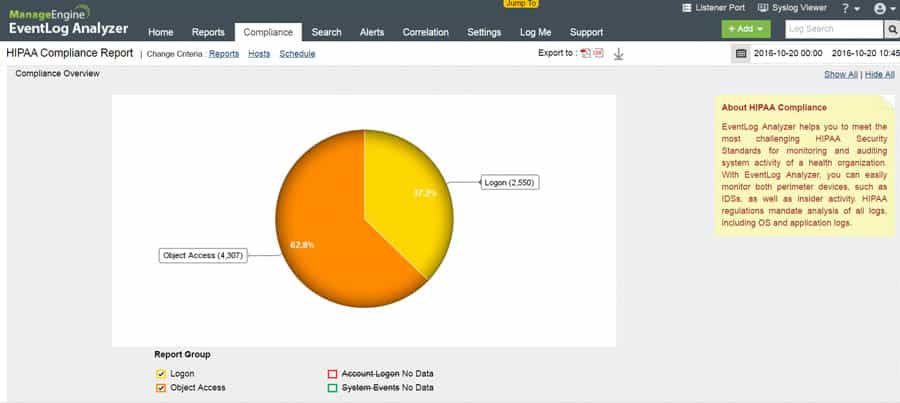
HIPAA Compliance Reports
The Health Insurance Portability And Accountability (HIPAA) regulation impacts those in healthcare that exchange patient information electronically. HIPAA regulations were established to protect the integrity and security of health information, including safeguarding against unauthorized use or disclosure of the data.
HIPAA states that a security management process must exist to protect against “attempted or successful unauthorized access, use, disclosure, modification, or interference with system operations.”
In other words, being able to monitor, report, and alert on attempted or successful access to systems and applications that contain sensitive patient information.
EventLog Analyzer meets the most challenging HIPAA Security Standards for monitoring and auditing system activity.
With EventLog Analyzer, you can easily monitor your network systems for any insider activity. HIPAA regulations mandate analysis of all logs, including OS and application logs.
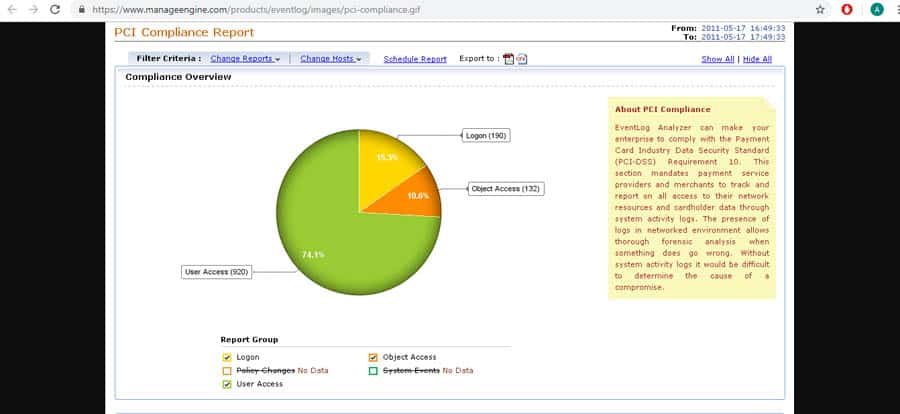
PCI Compliance Reports
EventLog Analyzer supports Payment Card Industry Data Security Standard (PCI-DSS) Requirement 10, which enables payment service providers and merchants to track and report on all access to their network resources and cardholder data through system activity logs.
The presence of logs in networks allows forensic analysis when something goes wrong. Without system activity logs, it would be difficult to determine the cause of a systems compromise.
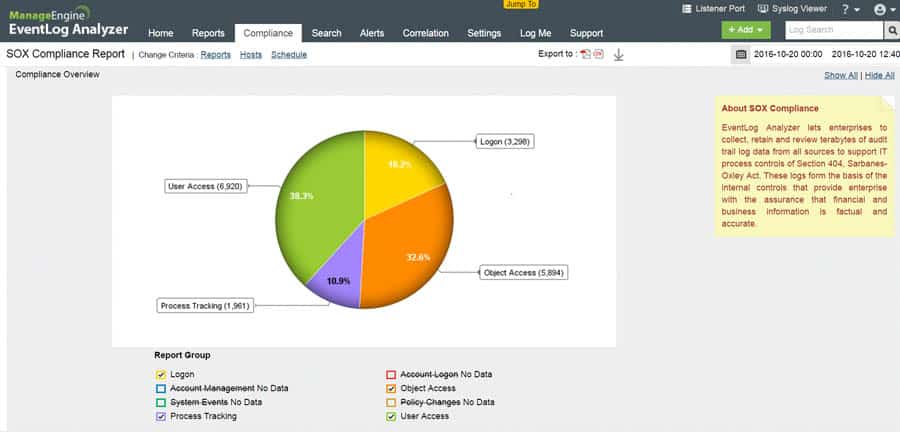
SOX Compliance Reports
EventLog Analyzer lets corporations collect, retain, and review terabytes of audit trail log data from all sources to comply with Sarbanes-Oxley Section 404's IT process controls.
These logs form the basis of the internal controls that provide networks with the assurance that financial and business information is factual and accurate.
Log Management Features
Log Collection
For event log collection, the EventLog Analyzer application does not require a separate agent on each host from which logs are collected.
Instead, the agent that collects Windows event log and Syslog messages is present as part of the EventLog Analyzer server itself. In this way, the tool performs event log collections task without introducing additional load on the hosts.
The EventLog Analyzer collects events generated by Windows and UNIX machines and logs by Cisco Switches and Routers without deploying an agent.
Setting up EventLog Analyzer to collect and report on events from a server, is a simple process for both Windows and UNIX systems. It’s also easy to set up the Cisco Switches and Routers to send the Syslogs to EventLog Analyzer.
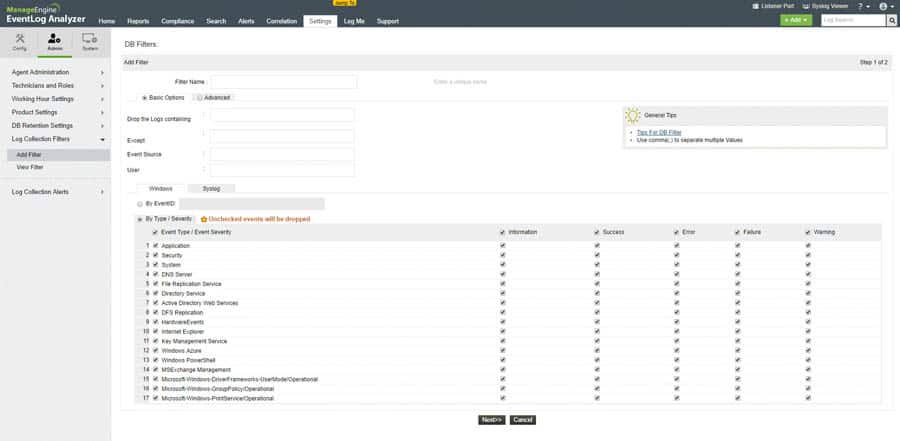
EventLog Analyzer lets you apply event filters on the collected event logs, before storing them in the database. With this feature, you can store only the necessary event logs in the database, making it easier to search for particular events, and optimizing the capacity of the database.
You can also create host groups to collect and report on specific hosts alone, which is useful when tracking event behavior and system performance for a selected group of critical servers.
EventLog Analyzer includes options to generate reports from simulated event log data. This lets you evaluate the capabilities of EventLog Analyzer as well as the performance of your server before collecting event logs in real-time.
Log Analysis
The EventLog Analyzer examines logs for all Windows, Linux and Unix systems, Switches and Routers (Cisco), other Syslog supporting devices, and applications like IIS and MS SQL. The tool is capable of performing real-time log file analysis and can also carry out an analysis of imported files. The files can be imported from the archive or any machine.
When a critical security event is undergoing on a machine in the network, the Even Log Analyzer collects, performs log analysis, and displays the event on the EventLog Analyzer Dashboard, in real-time.
The events log report is generated from the analyzed event logs. From the reports and graphs, you can drill down to the raw log events and do a root cause analysis within minutes, and then focus on resolving it.
Log Archiving
The Event Log Analyzer automatically archives all event logs and Syslogs collected from Windows, UNIX hosts, Routers/Switches, and other Syslog devices on the EventLog Analyzer server itself.
The event log archive is critical in forensic analysis and determining performance and usage statistics for a host.
The default log archiving interval creates a log archive file of all the received raw logs every 24 hours, and these log archive files are then compressed (zipped) after every seven days, to conserve hard disk space.
You can configure the archive file creation and compressed file creation any time depending on how often you need to archive event logs. You can even disable log archiving if required.
At any time, you can load event log archive files into the EventLog Analyzer database and generate reports from the archived event data.
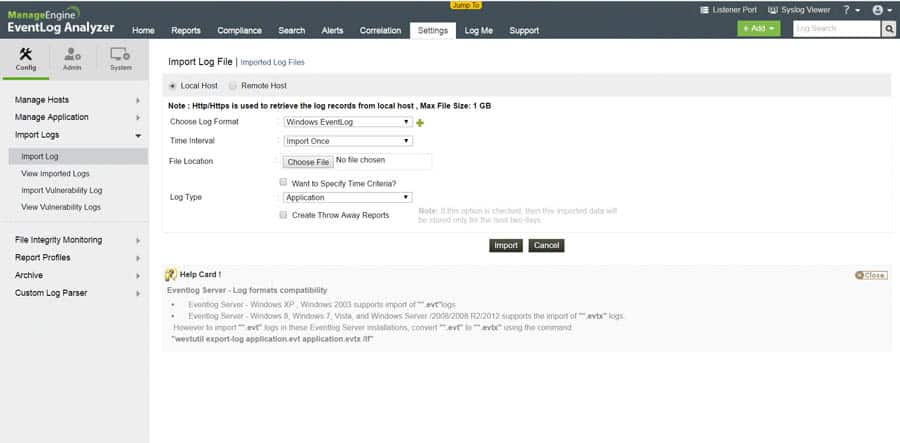
Importing Event Logs
EventLog Analyzer allows you to import and create reports on collected or historic Windows event log files.
The imported event logs are crucial in forensic analysis of log files and determining performance and usage statistics for a windows host which had already generated these logs.
Summary
It may be somehow easy to manage the amount of logged information in considerably smaller organizations, and a capable team of IT technicians may stay on top, but it’s still a waste of time.
There are several Event Logs Management tools available today, but the ManageEngine EventLog Analyzer is one of the best. It’s a must-have solution, as it prevents you from sorting through a large amount of data and helps keep your network run smoothly without dramatic outages or security issues.
Any environment today that lacks a reliable solution to handle the event logs is undoubtedly unaware of the situation and can land itself in trouble any time.
Download a free 30-day trial of Event Log Analyzer, now and test it in your network.