Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
Best Host-Based Intrusion Detection Systems (HIDS) Tools & Software

UPDATED: October 7, 2022
A Host-based Intrusion Detection System (HIDS) is a network security system that protects computers from Malware, Viruses, and other harmful attacks.
Much like a surveillance or security alarm system installed in your home or office, it watches and alerts for possible break-ins and thieves.
These systems may not do anything to stop an intruder; they only sound alarms or let somebody know that there has been something unusual. But an alarm system can’t do anything to prevent the intruder, but your locks, gates, and security guards do.
In the telecommunications world, a HIDS is like your home alarm system.
It lets you know when a hacker is attempting to attack your network or perimeter, it detects unusual behavior in the host and sends immediate alerts. The IPS (Intrusion Protection System) is like your locks, gates, and guards, which prevent intrusion.
Here is our list of the best HIDS tools:
- SolarWinds Security Event Manager – EDITOR’S CHOICE This log message collector and consolidator mines log data for signs of security breaches to form a SIEM. Runs on Windows Server. Start 30-day free trial.
- ManageEngine Event Log Analyzer – FREE TRIAL This log manager also implements SIEM to look for compromised security in the IT system. Available in free and paid versions for installation on Windows Server or Linux.
- Open Source Security (OSSEC) A widely used, free host-based intrusion detection system that mines logs for indicators of unauthorized activity. Available for Windows, macOS, Linux, and Unix.
- Samhain A free host-based intrusion detection system that is implemented in two parts, clients to gather data from many endpoints, and a server to process that data centrally, looking for security incidences. Available for Linux and Unix and can run on Windows with Cygwin.
- Wazuh This tool is an alternative to OSSEC because it was developed from that code, which is open source and so freely available. Runs on Windows, macOS, Linux, and Unix.
- Advanced Intrusion Detection Environment (AIDE) An open-source host-based intrusion detection system that is free to use. This is a command-line utility for Linux, macOS, and Unix.
- Tripwire This command line tool is a host-based intrusion detection system and it is free to use. Installs on Linux.
- IBM Security IDS / Maas360 An intrusion detection system that is offered from a platform of system security monitoring options. This is a cloud-based system.
- Lacework A cloud security intrusion detection system that looks for anomalies in activities. This is a SaaS platform.
- Security Onion A free, open-source package that bundles together a range of other open-source systems and includes a host-based intrusion detection system, which is actually Wazuh, detailed above. Runs on Linux.
What is a Host-based Intrusion Detection System (HIDS)?
It monitors the host computer where is installed by detecting unusual intrusions or misuse of resources.
It logs all events and sends immediate notifications to a security administrator to take proper action.
The HIDS keeps track of the traffic going and coming to the host computer, but not traffic in the network.
It can also monitor crucial internal system files and detect any attempts to modify them.
HIDS checks whether something or someone has violated any of the security policies.
HIDS is not:
A HIDS does not prevent intrusions or attacks, just as an IPS does.
Although HIDS can be installed on network points such as routers or servers, they cannot monitor at the network level.
A NID (Network Intrusion Detection), on the other hand, can be installed in network intersection points and monitor traffic.
A HIDS does not filter incoming/outgoing traffic based on rules, the way a firewall does, or a Bandwidth monitor does.
A HIDS is not designed to stop attacks, it is best, however, in detecting all kinds of attacks and delegating the “prevention” to someone else.
How does a HIDS work?
The dedicated intrusion detection system monitors traffic for malicious activity or policy violations.
It detects known attacks by the specific actions they perform (signatures).
The HIDS analyzes traffic (much like a network traffic analyzer) and behavior that matches these signatures in real-time, in the host.
It can also detect unusual usage patterns with anomaly detection methods.
When the HIDS finds a match, it raises an alarm and notifies the administrator.
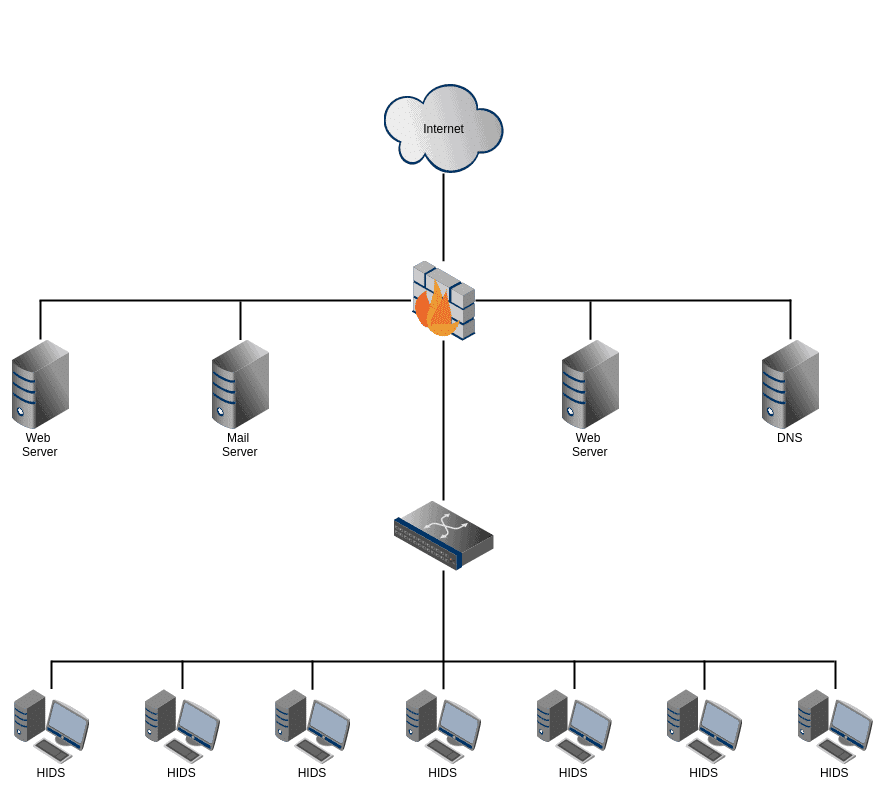
The HIDS is installed on the host, while the NIDS is placed inline.
The HIDS protects the system at the source so that it can be deeper and more intense in its security. The HIDS can also monitor system files, executables, and log files in the host computer and look for attack signatures.
Functionalities of a HIDS include:
- Anomaly-based detection
- Signature attack detection
- Zero-day attacks
- Traffic monitoring at host
- File integrity monitoring
- Log analysis
- Compliance and auditing
- Notification and alerting system
The 10 Best HIDS Tools & Software
Our methodology for selecting a host-based detection system tool
We reviewed the market for HIDS packages and analyzed options based on the following criteria:
- A log file collector
- A log consolidator and log file manager
- Log message sorting and searching for intrusion detection
- A data viewer for manual threat analysis
- The ability to exchange data with other security packages, such as SIEM tools
- A free trial for a no-risk assessment opportunity before buying or a free tool
- Value for money from a HIDS tool that provides competent detection measures or a free system that is thorough and worth using
With these selection criteria in mind, we identified a number of competent host-based intrusion detection tools, including many free packages.
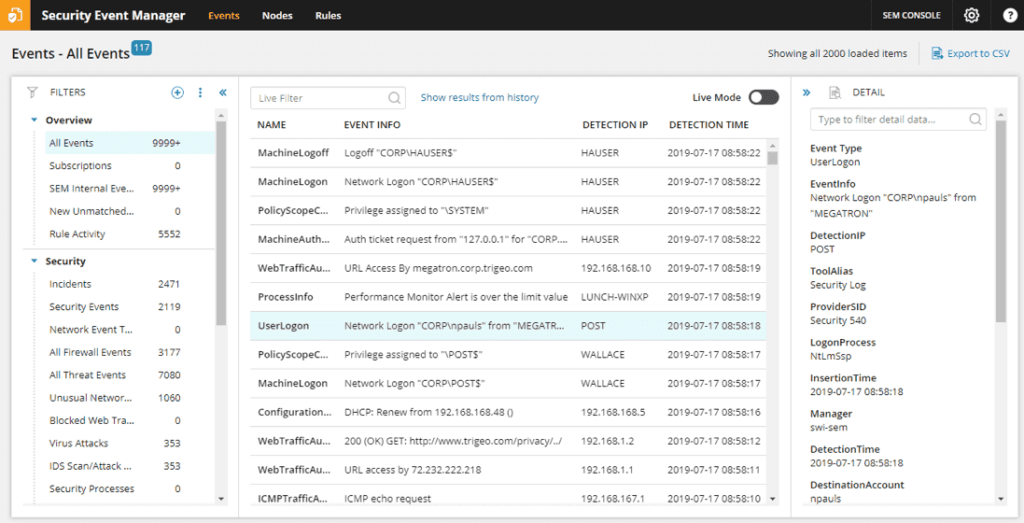
1. SolarWinds Security Event Manager – FREE TRIAL
The SolarWinds Security Event Manager (SEM) is a Security Information and Event Management (SIEM) software.
Features:
- Integrated compliance reporting.
- Automated threat remediation.
- Forensic analysis.
- File integrity monitoring.
- USB monitoring
- Forward log events raw data.
It can detect threats on a single host or the entire network.
SEM comes with a cyber-threat intelligence framework to identify suspicious activities and take informed actions.
SEM takes it beyond what a normal HIDS can do and provides some actionable capabilities.
The tool performs a powerful real-time event analysis, notifies you, or can respond actively.
It can block IPs, modify privileges, block USBs, kill applications, and more.
SEM can help you prove compliance for the following standards HIPAA, PCI DSS, SOX, and more.
It provides multiple out-of-the-box reporting templates to make auditing and compliance much more accessible.
Pros:
- Enterprise-focused SIEM with a wide range of integrations
- Simple log filtering, no need to learn a custom query language
- Dozens of templates allow administrators to start using SEM with little setup or customization
- Historical analysis tool helps find anomalous behavior and outliers on the network
Cons:
- SEM Is an advanced SIEM product built for professionals, requires time to fully learn the platform
EDITOR'S CHOICE
SolarWinds Security Event Manager is our top pick for a host-based intrusion detection system because it offers log management as well as security monitoring. This tool can gather together log messages from all across the system and even centralize log management for several sites. As logs get processed by the server, you see statistics and potential problems shown in the dashboard. If a series of suspicious events occur, the system raises an alert.
Download: Start 30-day Free Trial
Official Site: https://www.solarwinds.com/security-event-manager/registration
OS: Windows Server
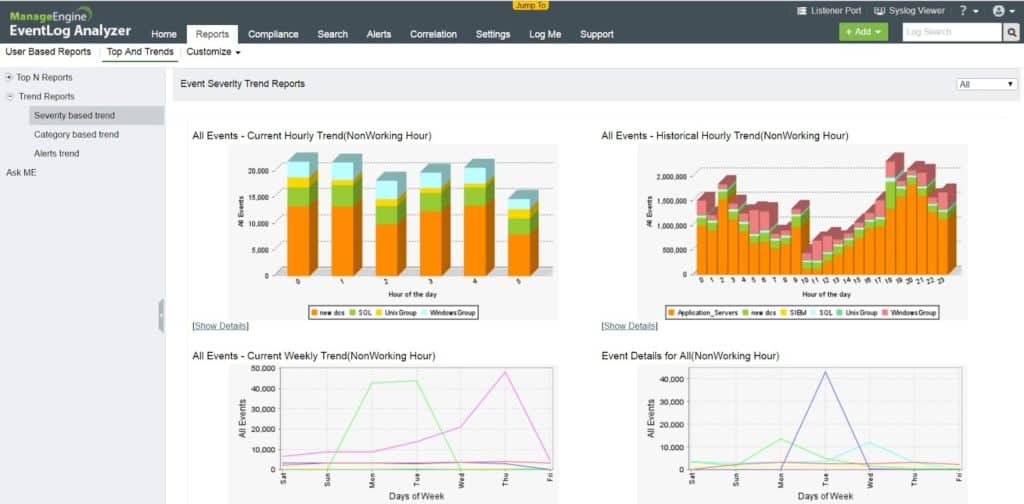
2. ManageEngine Event Log Analyzer – FREE TRIAL
The Event Log Analyzer from ManageEngine is more than a HIDS; it is a log manager, auditing, and IT compliance solution.
The tool can be used to perform network device audits, such as fire-wall audits, vulnerability scanning, and IDS/IPS reporting.
It can also be used for file server and application auditing.
The Event Log Analyzer’s SIEM capabilities allow you to monitor the integrity of your files in real-time.
This feature helps you protect sensitive information and meet compliance regulations.
You can track changes in files and folders from a central location and receive real-time alerts when there’s been a violation.
When it comes to log management, the Event Log Analyzer from ManageEngine is probably one of the most robust software out there.
It can collect logs, add secure storage, normalize, analyze, and create reports and alerts.
The tool also supports out-of-the-box IDS/IPS vendor logs, such as Cisco, Juniper, SonicWall, Barracuda, Fortinet, and more.
The Event Log Analyzer automatically collects all these logs and stores them in a central location.
Benefits of IDS/IPS Reports:
- Attacks in real-time or history.
- Most targeted devices.
- Trendy attacks, and more.
Price and License: The software comes in three editions, Free, Premium, and Distributed.
Pros:
- Customizable dashboards that work great for network operation centers
- Multiple alert channels ensure teams are notified across SMS, email, or app integration
- Uses anomaly detection to assist technicians in their day-to-day operations
- Supports files integrity monitoring that can act as an early warning system for ransomware, data theft, and permission access issues.
- Forensic log audit features enable admins to create reports for legal cases or investigations.
Cons:
- Can take time to fully explore the platform
The Free edition is limited for a maximum of five log sources, while the Premium and Distributed editions can handle from 10 – 1000 log sources and 50 – unlimited. You can start of with a 30-day free trial.
Download: Once the trial period is over, the software automatically reverts to the Free Edition of Event Log Analyzer and monitor a maximum of five log sources, perfect for a host-based environment. If at this stage you need the full functionality, you can purchase the software an activate all the features. https://www.manageengine.com/products/eventlog/download.html
3. Open Source Security (OSSEC)
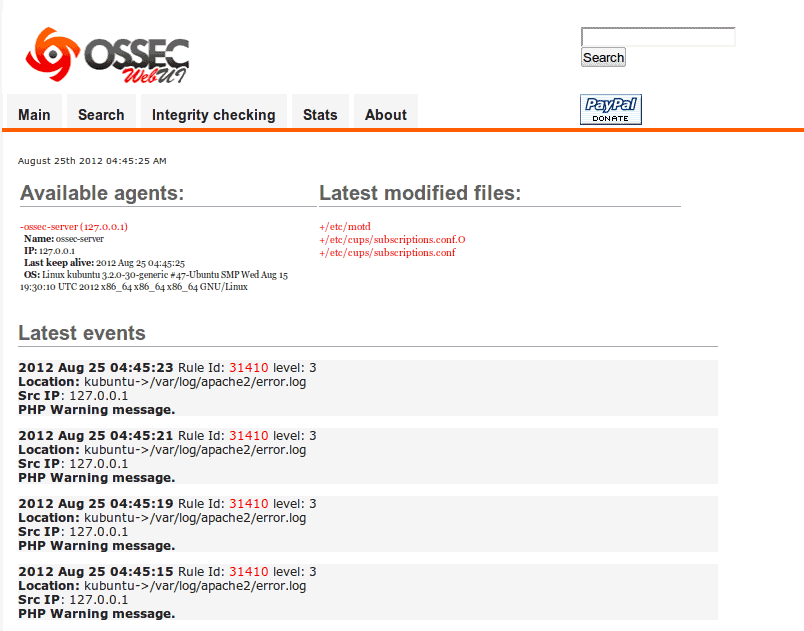
OSSEC (Open Source HIDS SECurity) is probably the best free, open-source, and multi-platform HIDS out there.
OSSEC provides the following functionalities:
- Log-based intrusion detection.
- File integrity monitoring.
- Compliance auditing.
- System inventorying.
- Windows registry monitoring.
- Rootkit and Malware detection.
- Centralized policy enforcement.
- Real-time alerting and active response.
The software comes with a robust correlation and analysis engine. It can monitor logs from multiple devices and formats and analyze their contents in real-time.
You can also manage different systems with OSSEC’s centralized management platform.
OSSEC takes the usual HIDS functionalities further with their active response system.
This system can respond to attacks and events in real-time using different mechanisms, such as firewall policies, integrations with third-party services, and self-healing actions.
This tool is compliant with the requirements of the Payment Card Industry Data Security Standard (PCI DSS).
OSSEC detects and alerts file system modifications or behavior that are PCI non-compliant.
OSSEC runs on most of the popular OS, like Linux, macOS, Windows, OpenBSD, FreeBSD, and Solaris.
Pros:
- Completely free and open-source
- Utilizes checksums to verify log and file integrity
- Supports root account monitor on Unix/Linux systems
- Strong community support offering new templates and scanning profiles
Cons:
- Reliant on the community for support
- Could use better reporting and visualization features
Price: Free and open-source.
Download: Get the latest stable version from the OSSEC official website.
4. Samhain
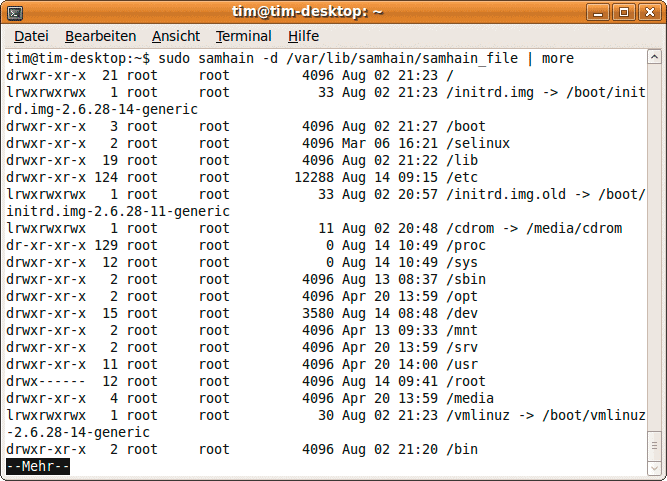
Samhain is another free and open-source HIDS tool.
Samhain provides:
- File integrity checking.
- Logfile monitoring and analysis.
- Port monitoring.
- Rootkit detection.
- Rogue SUID executables detection
- Hidden processes detection.
- Compliance with PCI DSS
It can be used as a standalone solution to monitor a single host, or as a centralized logging and maintenance platform for multiple hosts running different operating systems.
Samhain is a multiplatform application that supports Unix, Linux, and Windows (through Cygwin).
The software operates with a client/server architecture.
The clients can export logs to a central repository, get client configurations, or update from a baseline database.
Clients can also output data using Syslog, Email, or RDBMS.
But as mentioned above, the Samhain can be used only to monitor the host computer.
Pros:
- Free open-source tool
- Can detect rouge processes as well as intrusions from log files
- Can monitor user access rights to detect privilege escalation and insider threats
Cons:
- No paid support options
- Not available for Windows operating systems
- Interface feels outdated and not easy to use
- Lacks robust community found in more popular open-source NID tools
Price: Free and open-source.
Download: Get the latest stable version of Samhain from its official website.
5. Wazuh
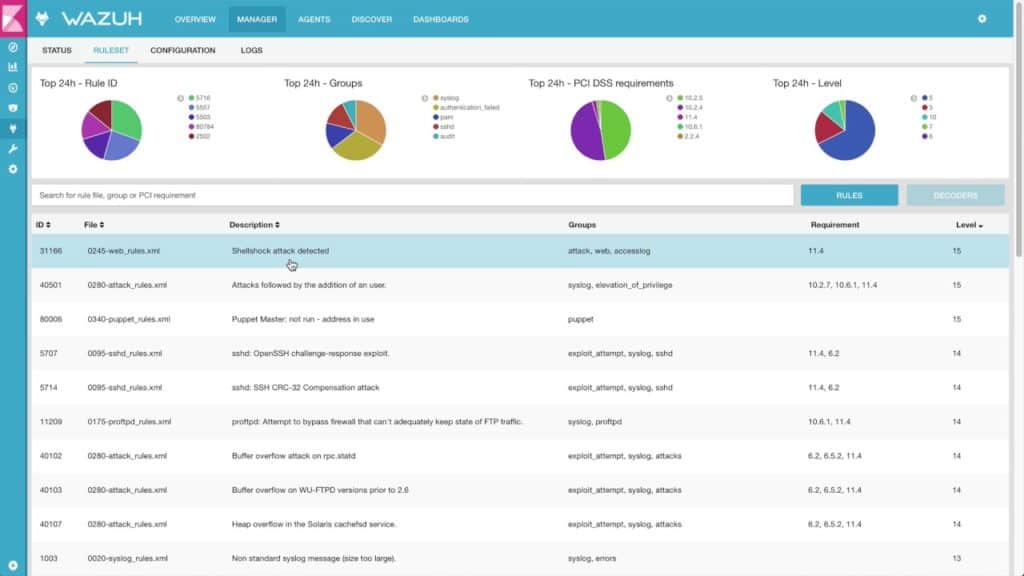
Wazuh, a fork of OSSEC, is a free and open-source HIDS.
Key Features:
- Log data analysis.
- File integrity monitoring.
- CVE databases to detect vulnerabilities.
- Windows registry monitoring.
- Malware and rootkit detection.
- Configuration assessment.
- Alerting and active response.
- PCI DSS compliance.
- Cloud and container security.
It comes with a centralized, cross-platform architecture that allows multiple systems to be monitored.
It can detect intrusions for popular OSs like Linux, Windows, macOS, FreeBSD, OpenBSD, and Solaris.
Wazuh uses client/server architecture.
The server uses an extensive database of signature attacks to identify intrusions and its detection engine to analyze log data.
Its lightweight multi-platform agents (clients) scan the target systems looking for rootkits, malware, or any suspicious behavior.
They can also detect hidden files, cloaked processes, or any incompatibilities with system calls.
Pros:
- Is a lightweight fork of OSSEC
- Integrates into platforms like ELK for a simpler workflow
- Using a range of technologies to identify indicators or compromise
- Supports in-platform data visualization
Cons:
- Is fairly comprehensive and can take time to fully understand/explore
Price: Free and open-source.
Download: Download the free Wazuh HIDS from the GitHub project.
6. Advanced Intrusion Detection Environment (AIDE)
Advanced Intrusion Detection Environment (AIDE) is a free and open-source HIDS.
Pros:
- Free open-source software
- Designed for security professionals
- Extremely lightweight deployment
Cons:
- Only available for Linux and Unix operating systems
- Not beginner-friendly
- Utilizes command-line interface for most actions
- Lack many features found in other NID tools
AIDE is designed only for checking the integrity of files.
With this tool, you can craft rules that create a database of files that are protected from intrusion.
When you first run AIDE, you generate this baseline database, which is checked frequently against the system.
The software will correlate and find differences between the database baseline and the filesystem.
You can check the following file properties:
- File type
- Permissions
- Inode
- Modification time
- File contents
- Number of links
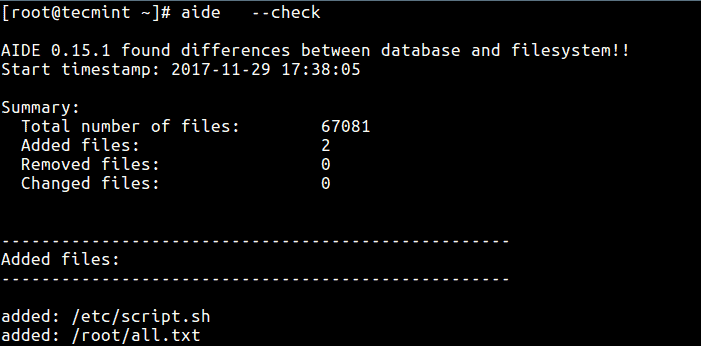
AIDE offers full flexibility when checking the integrity of files.
It allows you to write customized expressions to include or exclude files and directories from the monitoring process.
The software only has robust file integrity checking; it does not perform other HIDS functionalities like log-analysis or rootkit/malware detection.
Price: Free and open-source.
Download: Get the AIDE from the Github project.
7. Tripwire
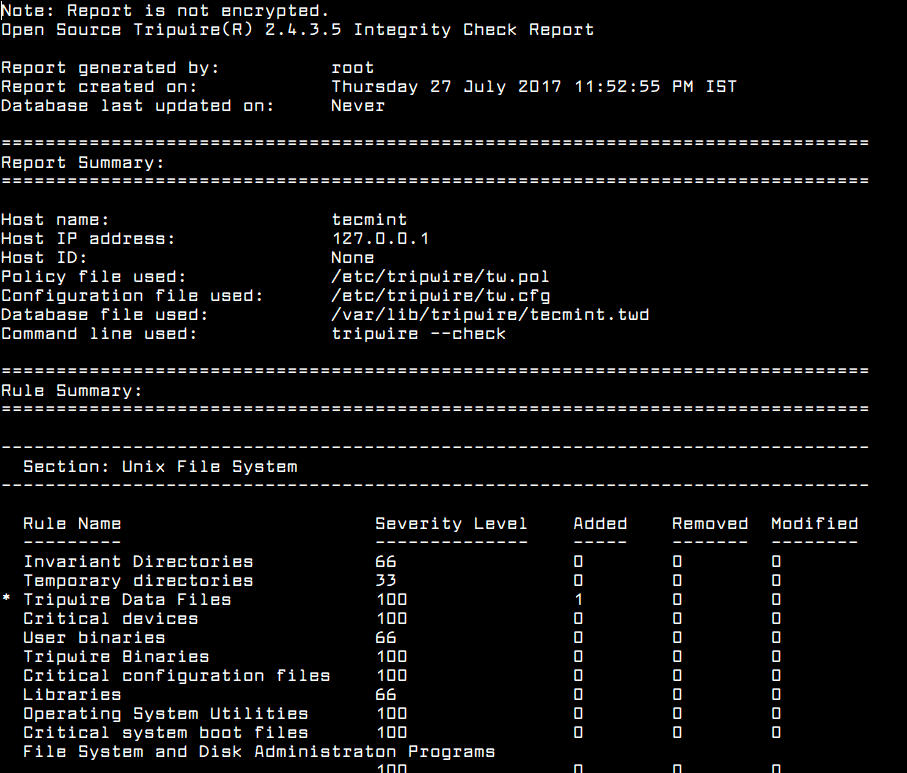
Tripwire develops a wide range of security and compliance software solutions.
Tripwire HIDS features:
- File integrity monitoring.
- Create system reports.
- Alerting through Email.
They offer a free and open-source HIDS that is capable of checking the integrity of files and send alerts when there's been file change.
When you start with Tripwire for the first time, you'll need to create a file baseline state by configuring a policy file.
This policy file contains information about which files or folders to check and the attributes, such as permissions, type, hashes, etc.
The software will continuously compare the current filesystem state with this baseline. When it detects a difference in a filesystem, it will initiate an alert.
You can also generate detailed reports that contain information about files, directories, devices, configuration, drivers, utilities, etc.
Pros:
- Supports real-time monitoring
- Can scan for vulnerabilities as well as detect and alert to config changes
- Better suited for larger networks
Cons:
- No free version – only free demo
- Interface could use improvement
Price: Free and open-source.
Download: Download Tripwire HIDS open-source from the Github’s project.
8. IBM Security IDS / Maas360
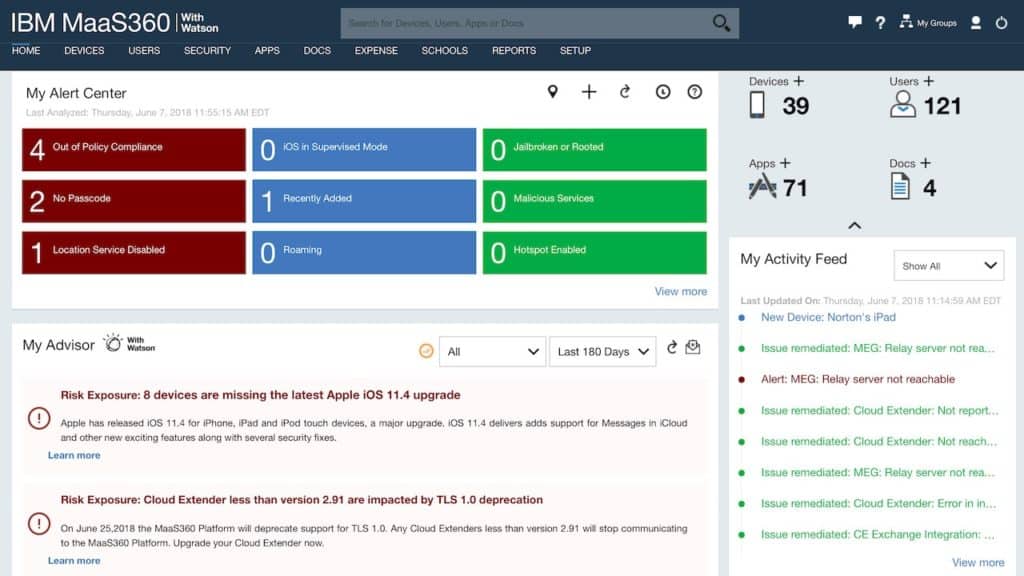
IBM is one of the oldest security providers in the market.
Pros:
- Provides a multitude of services designed for frictionless IAM
- Offers SSO, MFA, and access control from a single dashboard
- Generous 90-day trial
Cons:
- Many features cater to larger businesses – smaller organizations may not use all features and tools
It provides integrated security solutions to protect IT assets from threats. The IDS/IPS management module offers comprehensive monitoring, analysis, and management for your network.
The IBM IDS provides both HIDS and NIDS capabilities.
The service can detect intrusion in the network and “extrusions” from the host.
With this service, you can create and manage advanced policies to monitor threats efficiently.
You can also collect logs from different IDS/IPS vendor devices and view them in the single portal.
IBM IDS systems can detect different types of threats in a host or network, such as attacks, extrusions, scans, traffic regulation, and dynamic throttling.
Key Features:
- IBM X-Force® threat analysis service
- Define IDS policies (Attack, Scan, Traffic)
- Intrusion Detection Events page
- Real-time intrusion and extrusion detection notification.
IBM offers a variety of products that can detect intrusions at the host and network level.
Their Security SaaS can help you detect threats at the cloud, and their Mainframe security product can help you detect intrusions on the on-premises.
One of the products that offer real-time threat detection, insights, and remediation for endpoints is IBM’s MaaS360.
This product is an AI and cloud approach to unified endpoint management.
Price: IBM MaaS360 comes in four different editions.
- Essentials ($4.00 per device/month)
- Deluxe ($5.00 per device/month)
- Premier ($6.25 per device/month)
- Enterprise ($9.00 per device/month)
Download: Get your free trial of IBM MaaS360 for 30 days!
9. Lacework
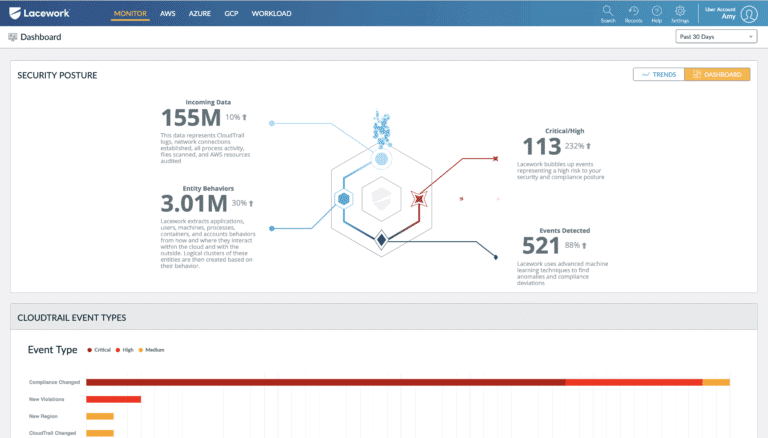
Laceworks develops advanced end-to-end cloud security solutions that allow you to view the risk across workloads on the cloud or containers.
Pros:
- Provides a highly visual look at your risk over different platforms
- The dashboard is simple and easy to navigate
- Can help adhere to compliance requirements such as PCI DSS and HIPAA
Cons:
- Not the best option for managed service providers
One of their products if the anomaly-based Host Intrusion Detection System (HIDS).
This solution can identify any unusual activity that is happening across workloads and accounts in the host.
The Lacework comes with an easy to navigate dashboard.
It shows incidents at a high level of details.
From this dashboard, you can visualize the interactions between cloud entities and search for events anywhere across the cloud.
With Lacework, you can detect abnormal changes in behavior and threats across your workloads, containers, and the cloud.
Lacework can also help achieve compliance for regulations such as SO2 2, PCI DSS, HIPAA, and others.
Key Features:
- Visibility into cloud accounts, microservices, and workloads.
- Comprehensive data collection.
- Powerful alerting system.
Price: For more information on Lacework pricing, get a quote.
Download: Get your fully functional free trial of Lacework for 30 days.
10. Security Onion
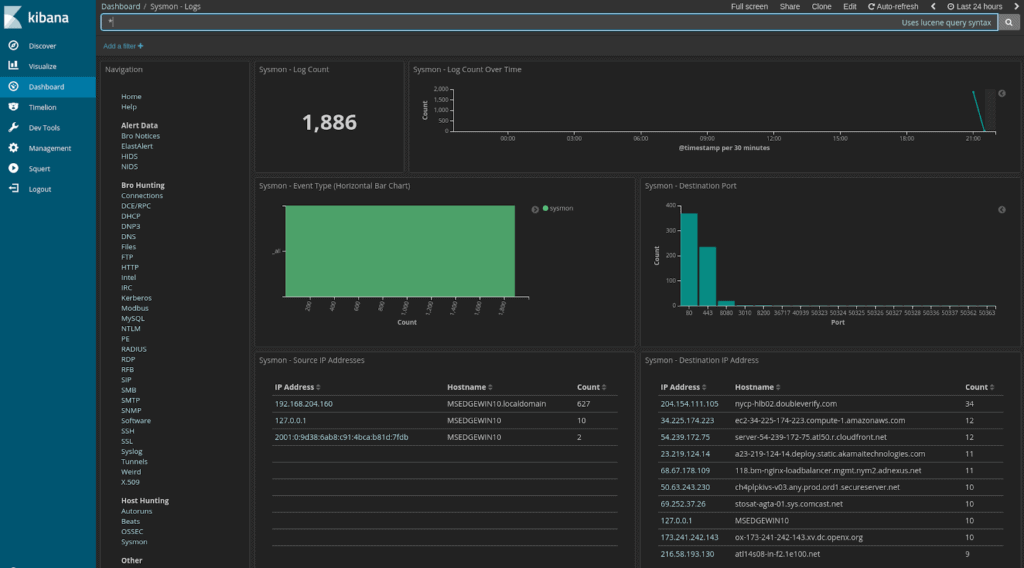
Security Onion is a free and open-source Linux distro for Network Security Monitoring (NSM), IDS, and log management solution.
Tools that Integrate with Security Orion:
- HIDS alerts with Wazuh and OSSEC.
- NIDS alerts from Snort and Suricata.
- Full packet capture with netsniff-ng.
- Analysis-driven NIDS with Bro.
- Host data through Beats, Wazuh, syslog, and more.
- Session data with Bro.
- Visibility into the event data with Sguil.
- Deep data analysis with Kibana.
- Analyze and visualize NIDS/HIDS alerts with Squert.
It contains a wide range of security tools, including HIDS functionalities.
It integrates three core components, full packet capture, NIDS/HIDS, and analysis tools.
With Security Onion, you can create and deploy multiple distributed sensors in your enterprise network.
The sensors see and store as much information as possible from these security tools.
Security Onion integrates with other open-source security tools to achieve this high level of protection.
Tools such as Snort, Suricata, Bro, Wazuh, OSSEC, Sguil, CyberChef, Squert, Kibana, NetworkMiner, Elasticsearch, Logstash, and more.
Pros:
- Free open-source software
- Designed for security professionals
- Features built-in packet sniffer for live traffic analysis
Cons:
- Only available for Linux
- Uses Kibana for visualization which can be complicated for newer users
- The interface is complicated and not user friendly
Price: Free and open source.
Download: Security Onion from the GitHub project.
Conclusion
NIDS don’t have the advantage over HIDS.
Although NIDS can look at incoming and outgoing traffic and detect intrusions at a network-level, they don’t have the grain-level security that HIDS can provide at the host.
HIDS can detect attacks that do not involve the network; they can monitor changes in critical system files, and even analyze what an application is doing.
There are tons of security solutions, from SIEM, NIDS, HIDS, NIPS, etc.
Trying to select the appropriate software can be overwhelming. They all have the same goal of protecting your network and servers, but they do it differently.
Nearly all of the “10 best HIDS tools shown” here are full HIDS tools, but there are some that fall into the SIEM category.
They can do pretty much everything, including HIDS functionalities.
There are a variety of commercial, free-license, free trials, open-source HIDS tools.
Most of them, like OSSEC, are open-source and free but more advanced software like SIEM that integrates everything comes with a price.
You can start with SolarWinds Security Event Manager and ManageEngine Event Log Analyzer which are great SIEMs, and offer free license.
Host-Based Intrusion Detection Systems (HIDS) FAQs
What is an example of HIDS?
Some of the best host-based intrusion detection system (HIDS) tools are free to use. This category includes OSSEC, Advanced Intrusion Detection Environment (AIDE), and Samhain. There is a fine line between HIDS and SIEM because the Security Information Management part of Security Information and Event Management is based on the collection of log files, the same as HIDS. Thus some systems that are HIDS are also defined as SIEM, Wazuh is an example of this phenomenon. SolarWinds Security Event Manager and ManageEngine EventLog Analyzer are two examples of paid HIDS packages.
What does a HIDS do?
A host-based intrusion detection system (HIDS) searches through collected log messages for signs of unusual activity. This activity might indicate the presence of an intruder or software introduced onto the system by hackers to gather information and steal data.
Is antivirus a HIDS?
Antivirus and HIDS operate in different ways. An antivirus system operates on one endpoint and looks for harmful malware. This can be implemented through the identification of the files of malware by examining each file’s characteristics and comparing them against a signature database. Antivirus systems have recently evolved into Endpoint Detection and Response (EDR) systems, which look for anomalous behavior on an endpoint. An EDR acts like a HIDS but operates on just one endpoint. A HIDS collects log messages from all devices connected to a network, centralizes them, and consolidates them into a common format so that they can be held in a single database and searched for signs of anomalous behavior.