Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
How To Lockdown USB Ports?

UPDATED: September 23, 2022
Disabling USB ports is the best way to prevent network users from using external USB-based devices such as USB drivers or pen drives and taking valuable, sensitive data.
If many people use your computer- such as a shared system at work- people can easily insert their USB flash drives into your system. These USBs may contain infected files or malware, which can infect your computer. Not only this, but someone can quickly steal unauthorized data to and from the flash USB drive. Blocking the USB port on a single computer can quickly be done through the BIOS or at the hardware level, but when system admins need to block USB ports from hundreds to thousands of computers, things might get complicated.
In this step-by-step post, we'll go through six simple methods to lock down USB ports. You can use the following methods to disable USB ports in Windows 7, Windows 10, and other systems. We'll also show you a method to lock down USB ports for networks of computers.
Why Lock Down USB Ports?
Locking down USB ports is an effective strategy against unauthorized attachment of removable storage devices to the system via USB ports. If there is unattended use of removable devices, your system may become vulnerable to a malware attack or data theft. Blocking USB ports prevents any unidentified USB devices from connecting to your endpoints.
a. Data Theft Prevention
A shared system is the easiest target for data theft, especially in the workplace. Since employees have access to inside information and system operations, they have a high chance of stealing data without anyone knowing.
It is very common that when employees leave an organization, they often take with them the company's sensitive information. Disabling USB ports prevent people from plugging their drives and copying sensitive information- such as company secrets and customers' data.
Moreover, with unsupervised USB access, a disgruntled employee or hacker could install malicious software on your system. So, locking down USB ports safeguard your computer device and data.
b. Safety From Malware
External devices could contain malware, such as viruses or infected files. When someone unintentionally attaches such a device to the endpoint via a USB port- the computer and entire network could get infected.
The owner may or may not know about the malware in the USB. Also, screening a USB may not be enough since the virus lies in the firmware. Thus, blocking USB ports secure your system's safety by inhibiting any malicious file transfer.
Method 1: Using Group Policy
The first simple method on how to lock down USB ports is using Group Policy Object (GPO).
- On your desktop, click on the Windows button. Type Run in the search bar.
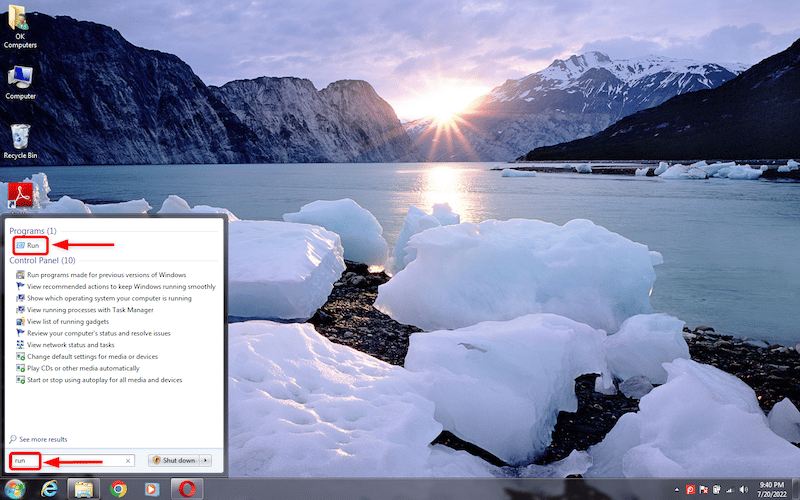
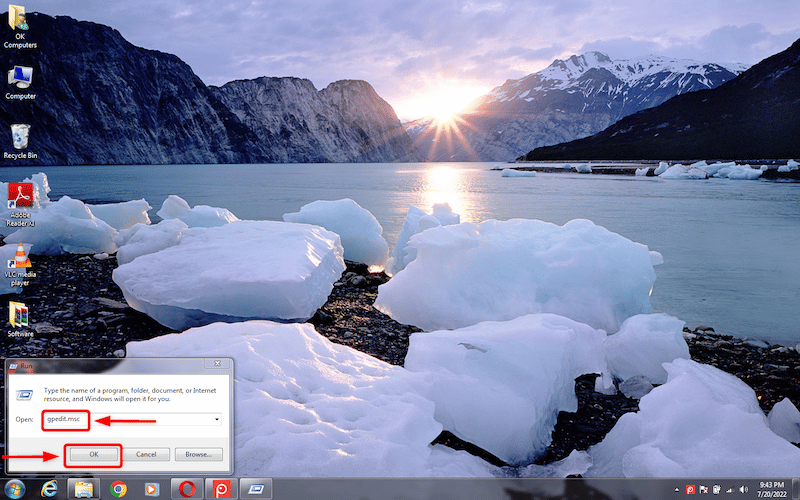
- Click on Run in the search result to open the “Run” utility. Then, type “gpedit.msc” and click Ok. This will open the Group Policy editor.
- Go to “Computer Configuration” > “Administrative Templates” > “System” > “Removable Storage Access”.
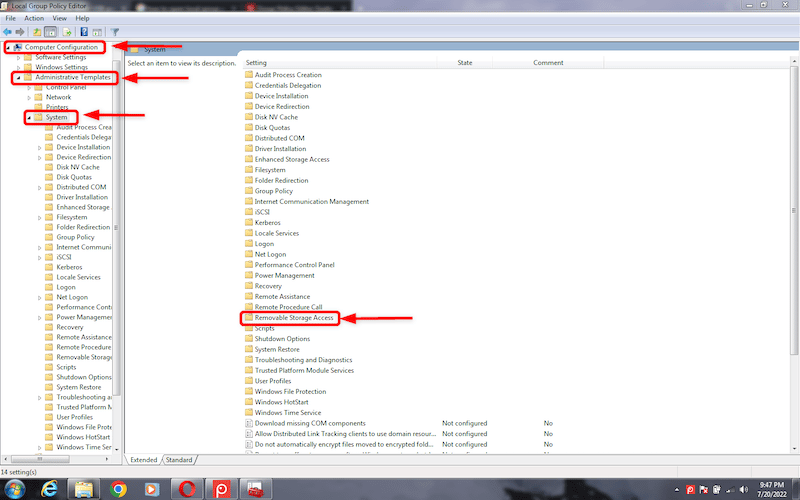
- Find All Removable Storage classes: Deny all access in the right-hand panel. Double-click on it to open a tab for editing.
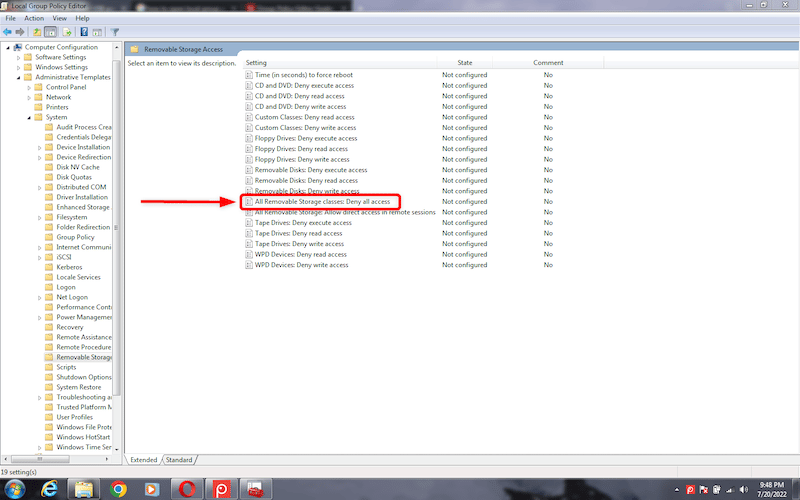
- In the editing tab, click on Enabled and then click on Apply to save the changes.
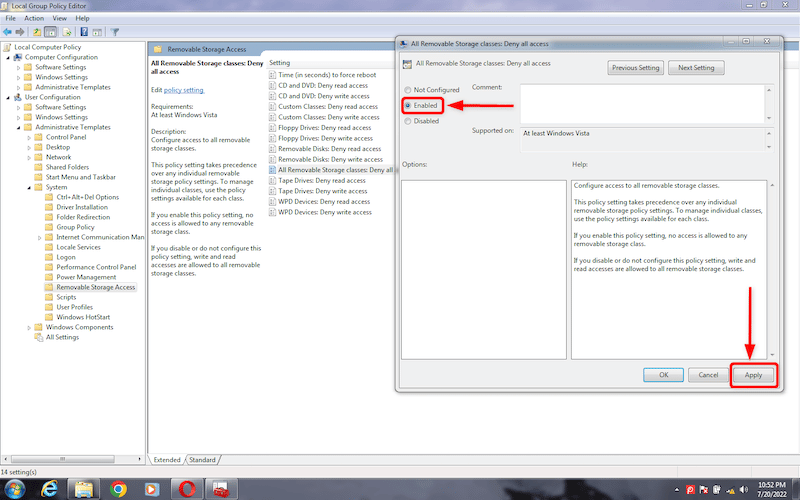
Your system's USB ports are now unable to recognize external storage devices.
Method 2: Using Windows Device Manager
You can also lock down USB ports via Device Manager. The following steps will prevent other users from attaching their flash drives to your system.
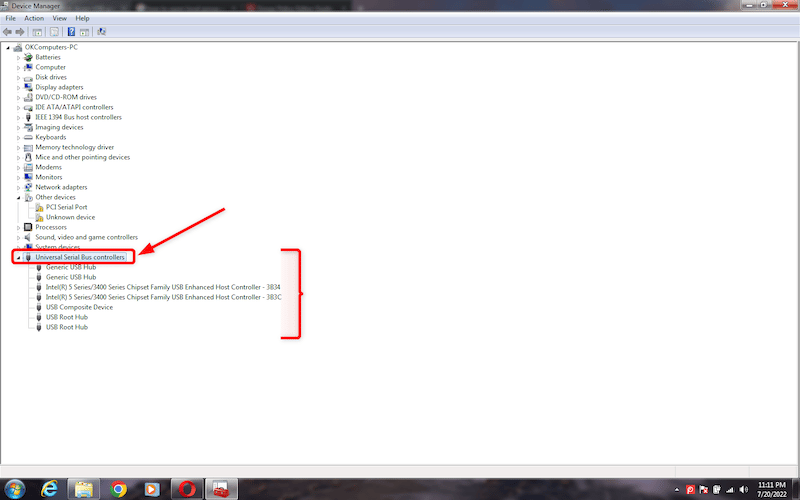
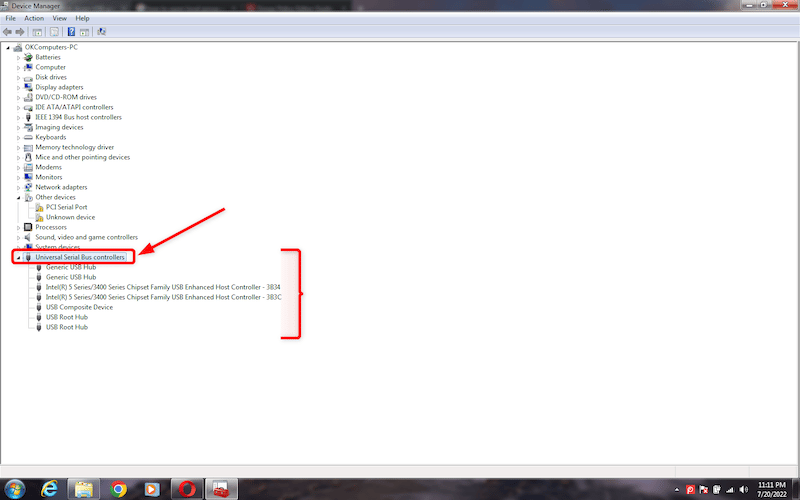
- Click on the Windows button to open the “Start menu”. Type “devmgmt.msc” in the search bar to open Device Manager.
- Click on the Universal Serial Bus Controllers. It will open a list of USB ports.
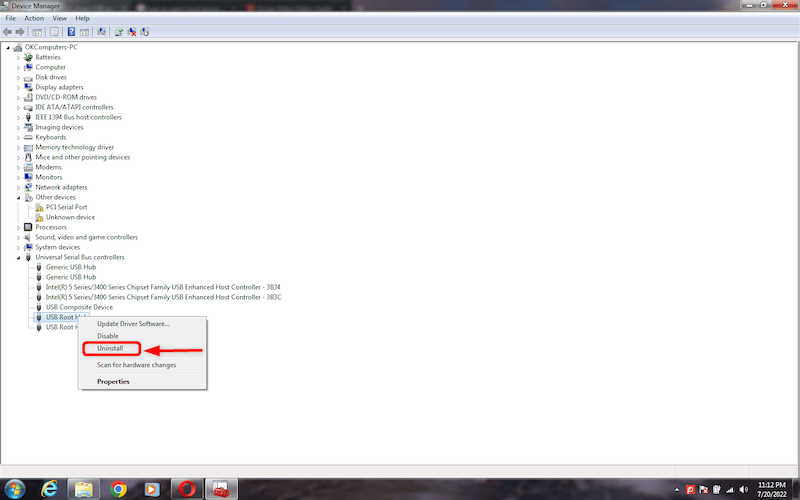
- Right-click on any USB port and then click on Disable to disable the port.
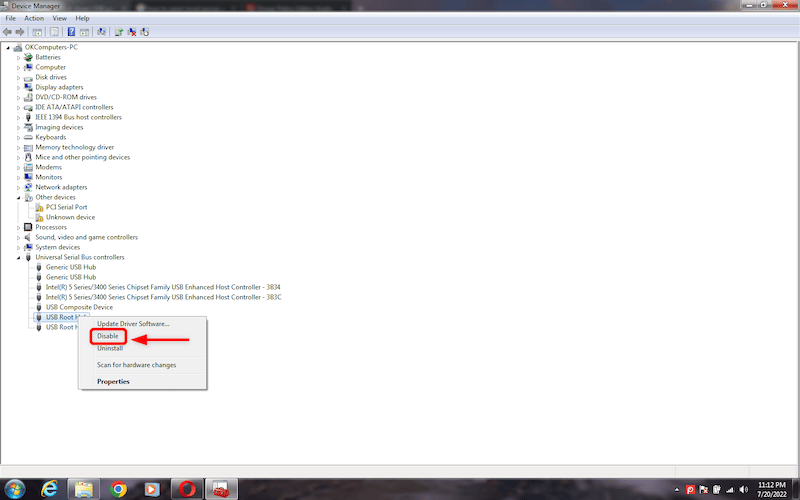
This action will block all the ports on your device so no unauthorized USB drive can make its way.
Method 3: Disable USB Ports From Registry
| Note: Any change in the Registry Editor may cause permanent changes in your system settings. So, make sure to back up before making any changes. To take a backup, go to File and click on Export. Now, save the file to an accessible location on your computer. |
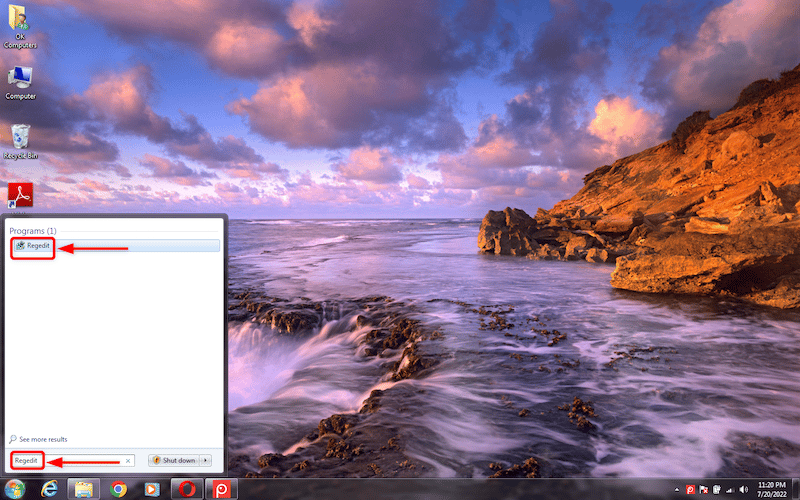
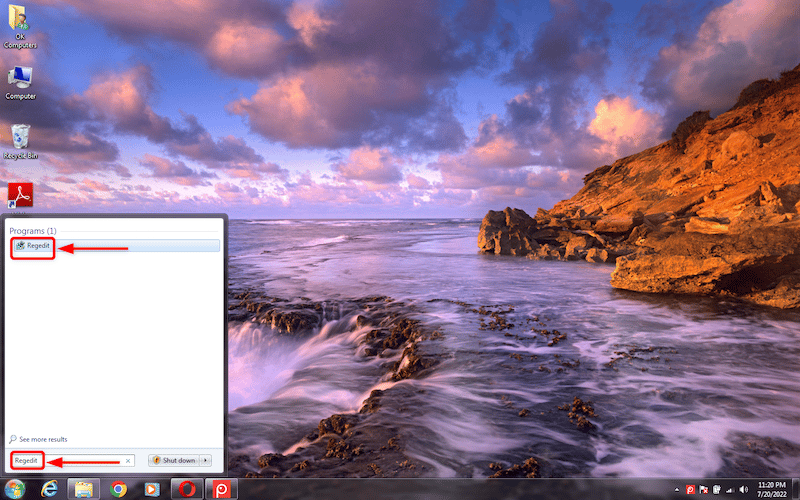
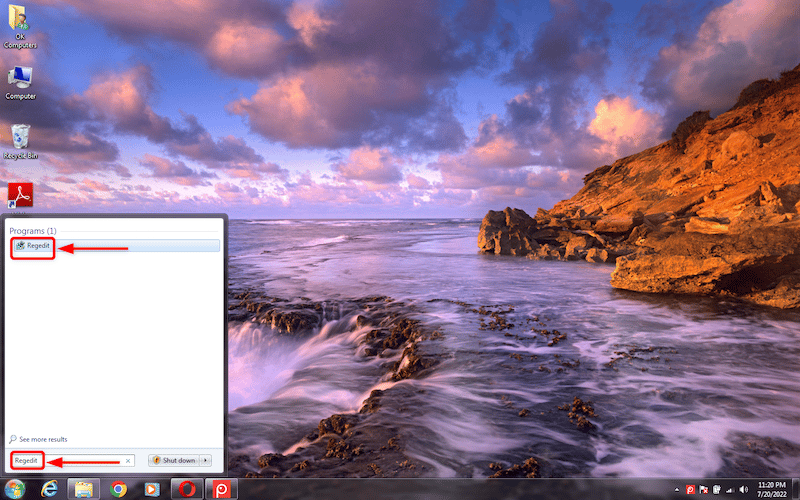
- Open the start menu by clicking on the Windows button.
- Type “Regedit” in the search box to open the Registry Editor.
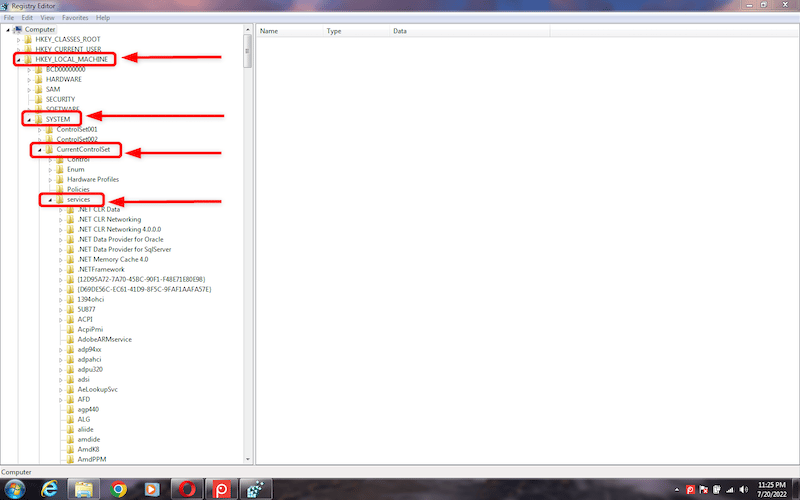
- In the Registry Editor, open the folder “KEY_LOCAL_MACHINE\SYSTEM\CurrentControlSet\Services\USBSTOR”
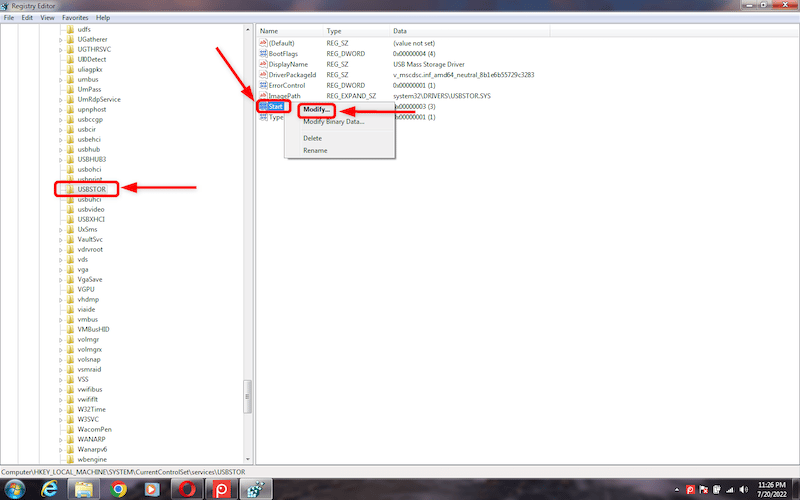
- In the USBSTOR, navigate to “Start”. Double-click on Start to open a sub-menu. In the sub menu, click on “Modify” to edit the value.
- A small pop-up window will open. If the value appears as 3, then the port is enabled. Change the value to 4 to disable the USB port. Click OK to apply the changes.
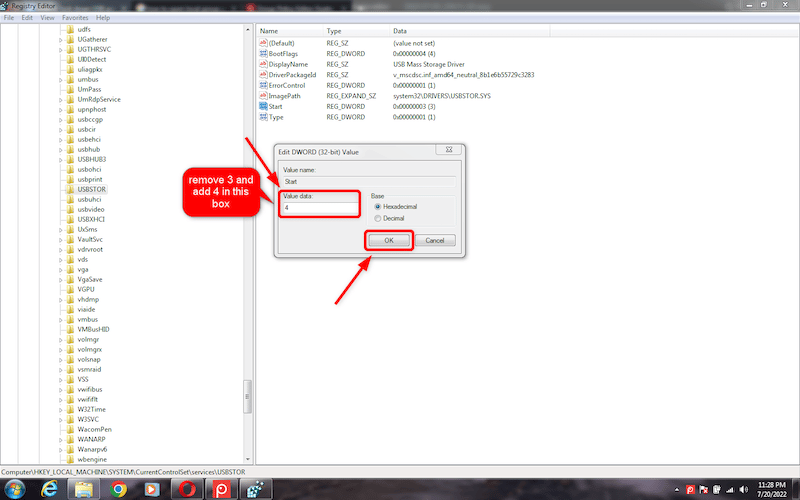
- Close the Registry once the process is completed.
This method of locking down USB ports produces permanent changes in the system. Thus, it is advised to do it under technical guidance.
Method 4: Uninstalling USB Mass Storage Drivers
Another method to prevent data leakage from USB ports is to uninstall the USB Mass Storage Drivers. Follow these steps to lock down the USB ports in your system.
- Click on the Windows button to open the Start menu.
- Open “Device Manager” by typing “devmgmt.msc” in the search bar.
- In the Device Manager, click on the Universal Serial Bus Controllers to get a list of USB ports.
- Right-click on the USB port to uninstall the driver. This action will indirectly lock down the USB port.
If you want to enable the USB ports in the future, you will have to re-install the USB Mass Storage Driver.
Method 5: Disconnect USB Ports at the Hardware Level
It is impossible to disconnect all the USB ports from the motherboard. However, you can easily disable the ports on the front and top of the computer.
Plug out the cable from the USB header to disconnect the ports from the motherboard. Thus, you can remove any risk of unauthorized use of these ports by anyone.
Method 6: Third-Party Software
The safest and most reliable method of disabling USB ports is by using third-party software. There are countless tools available for USB port lockdown. This software identifies and blocks all unidentified USB devices and provides access to trusted devices to attach to your system.
CoSoSys Endpoint Protector offers one of the best DLP (Data Loss Prevention) solutions. It is an excellent option for business network/ system admins wanting to control and monitor USB usage for all endpoints.
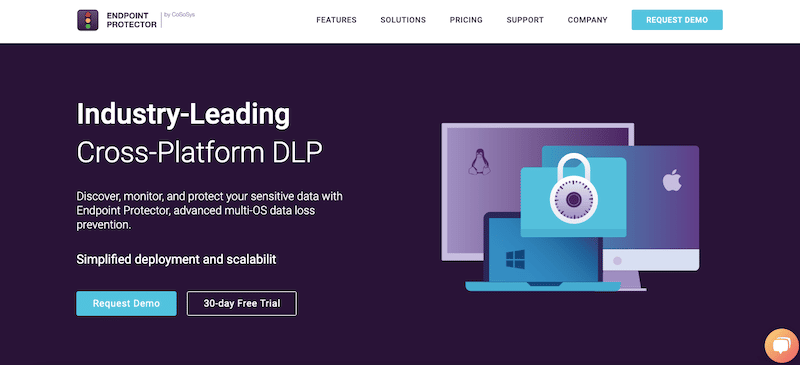
With CoSoSys Endpoint Protector, you can block the USB ports of all employees from their endpoints, including laptops, desktops, and servers. CoSoSys Endpoint Protector offers a high-performance Data Loss Prevention (DLP) solution with tools like device control, content awareness, encryption, and eDiscovery.
The Device Control module of CoSoSys Endpoint Protector controls all the portable USB devices connected to the computers. It also monitors the transfer of data across authorized devices. Not only USBs, but you can also control CD/DVDs, Bluetooth, Printers, iPhones, iPad, WiFi, and Serial Ports. You can allow or deny access to these devices by changing the settings. CoSoSys Endpoint Protector also offers a “Read-Only Access” to using a USB without allowing copying data.
With an endpoint control solution like CoSoSys, you can control these devices on a;
- Global level (all devices)
- Group level (devices in a particular group)
- Individual computers or users
CoSoSys Endpoint Protector provides security solutions for multiple operating systems, including Windows, macOS, and Linux.
CoSoSys Endpoint Protector features
CoSoSys offers essential features like file tracing and shadowing to view and monitor user activity. It also comes with DLP for in-motion and at-rest data and file/sensitive data password security. CoSoSys Endpoint Protector’s DLP solutions safeguard your company's network even when employees work remotely. It offers endpoints security, compliance scanning, and action against security policy violations.
CoSoSys Endpoint Protector also provides high-end data safety. From Intellectual Property (IP) to Personal Identifiable Information (PII), so you can secure all sensitive data on your employees' endpoints and comply with strict regulations and industry standards.
How to start with CoSoSys Endpoint Protector?
To start with CoSoSys Endpoint Protector, you can register and get a 30-day free trial or request a free demo. You can deploy Endpoint Protector on-site through a virtual appliance or as a standalone software package. You may also run the software via its cloud-based service or SaaS.
Frequently Asked Questions
What is USB port lockdown?
USB port lockdown is a secure method to prevent the attachment of unidentified external storage USB devices to your endpoints. Unmonitored connectivity with external devices puts your system at risk of malware attack and data theft. Locking down USB ports on a computer or endpoint helps prevent employees or unknown people from attaching USB flash drives.
Should I lock down my USB ports?
Yes, it would help if you locked down the USB ports of your computer system. It not only protects your computer from data leakage but also infected files. USB port lockdown is an efficient data protection solution for a shared computer at work, at home, or on a network of endpoints.
Can I disable the USB port by uninstalling the driver?
Yes, you can. Go to Device Manager by typing “devmgmt.msc” in the search bar. Expand Universal Serial Bus Controllers to generate a list of USB ports. Right-click on a port, click on Disable, and confirm by clicking Ok on the pop-up. You can also uninstall USB Mass Storage Driver to lock down a USB port. Keep in mind that you would have to reinstall it anytime you need it in the future.
Can I block other USBs but give access to mine?
The manual methods of locking down USB ports do not allow partial blocking; they would lock USB ports for all USB devices. However, there is third-party USB blocking software that can recognize USB devices based on hardware, helping you to create lists of allowed devices and blocked devices based on type, brand, etc.
What are USB port blockers?
A USB port blocker is a device that helps you deny access to any USB port. It prevents USBs or external storage devices from attaching to a computer system or server. Thus, it inhibits copying sensitive data, transferring malicious files, and charging mobile devices.



