Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
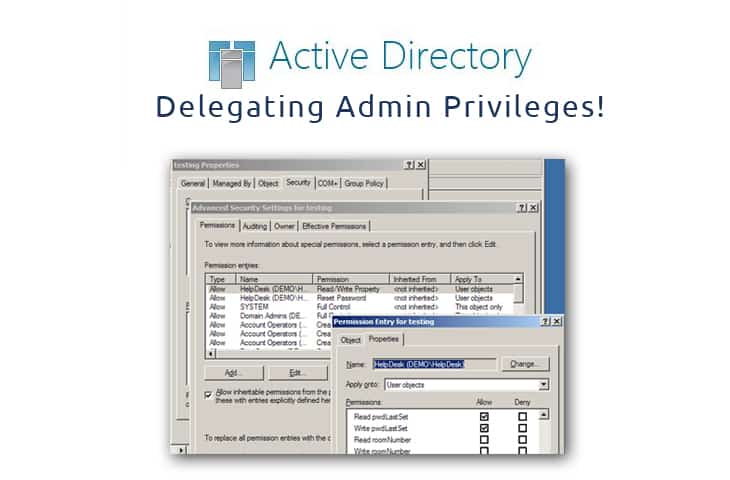
Delegating Admin Privileges and Managing Risk within Active Directory
UPDATED: January 20, 2020
There are numerous reasons for having to delegate administrative privileges to standard users in a domain; including maintenance and the installation of a software programs.
Recent surveys have shown us that the majority of security breaches occur through privileged user accounts.
It is therefore very important that accounts with any kind of privilege are protected.
We'll go through a few things you can do to manage the security risk when delegating administrative privileges.
Do Not Add Users to the Domain Admins Group
If administrative privileges have to be delegated to standard users, you do not need to make them members of the Domain Admins Group.
You can either provide the credentials of shared privileged accounts or add them to Administrators, for example.
It is recommended to use a least privilege policy in a domain – e.g. one or two Domain Administrators, one or two shared privileged accounts or up to three temporary privileged user accounts.
Temporary Privileges
If the user needs administrative privileges to perform specific tasks, you can assign them temporarily for a specific period of time.
Just make sure you remember to revoke these privileges once the assigned task has been completed.
Auditing
Network Admins should have a pro-active and continuous method of auditing and monitoring privileged user accounts – either through native auditing methods (powershell scripts, etc) or by deploying automated solutions.
By doing this you will be able to keep track of users with administrative privileges, the duration they have been assigned the privileges and when their privileges are due to be revoked.
The activities and changes carried out by privileged accounts should also be monitored.
You will then be able to see the logon and logoff events of these user accounts and spot anything irregular.
Password Policies
The passwords of privileged accounts should be changed within 15 to 30 days – either manually or through an automated solution.
You can use one-time passwords for temporary privileged accounts. It is not recommended to use “never expire passwords” with privileged user accounts.
The passwords of any user account should not be stored in any documentation that can be easily accessed.
Backup and Recovery Plan
You should always make sure you are taking regular backups of the Active Directory and its objects.
In addition to complete backups of the server operating system, you should have a simple method for restoring the state of objects or changes.
You can either use native processes for this or you can deploy a third-party solution.
It is recommended to have an option that allows you to restore multiple deleted objects in seconds.
Deal with Obsolete Accounts
There should be a monthly analysis of obsolete accounts that remain inactive for 15 to 30 days.
These obsolete accounts should be promptly disabled and moved to a separate organizational unit.
You should also Delete such accounts after 45 to 90 days of inactivity, as such accounts could potentially be used by people with malicious intent.
This will ensure no accounts in AD are used for anything other than what they should be used for.
Session Recording
You can monitor and record the sessions of privileged accounts when they log on and perform any action on the server.
Manage Embedded Credentials
The login credentials of an administrator or privileged account can be stored in different scripts and service accounts.
These passwords should be handled carefully and updated regularly. If you have adopted an automated system to change the passwords automatically at scheduled intervals, then passwords stored in such scripts and service accounts should also be updated.
Direct Access
For extra security, you can deploy a solution that lets users access server components without showing them passwords or exposing other network/technical information.
There are numerous things administrators can do to mitigate risks stemming from delegating administrative privileges to users.
There are multiple ways the points in this list can be achieved – through native processes or by deploying third-party solutions.
Native methods for auditing configuration changes, monitoring user activities and many of the other points in this list can be complex and time-consuming.
For these reasons many organizations opt for third-party solutions like LepideAuditor Suite that simplify the process, providing a pro-active and automated means of auditing, monitoring and alerting on privileged user activity.
We recommend monitoring accounts that are privileged within your network if they must have those privileges – if not, remove them completely to ensure those accounts wont be targeted by hackers.



