Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
The Best USB Port Locking Tools

UPDATED: October 31, 2023
Restrict access to your USB ports to secure your network from data loss and USB-propagated viruses.
Your internal network security has always been at risk from removable hardware. Once such devices leave your network architecture, you can no longer trust their security once they return to your network. You are unable to ensure they haven't been exposed to vulnerabilities since during the time they were outside of your network, they were out of the reach of your security procedures.
Network administrators are in the constant conflict of preventing critical data loss and USB-based malware, while still enabling users to take their flash drives home. The simplest solution is to secure your USB flash drives because they are one of the main sources of such threats. For example, a computer may unintentionally pick up a virus that spreads itself to your USB flash drives, but this form of threat need not originate from a USB flash drive and can instead originate from any place in your network.
This means that to be safe, you need to attack the problem from both external and internal perspectives: you need to protect your company's USBs and any devices that might connect to them. There are several ways that you can do this, but one of the simplest ways is through the application of USB control software. This software can help you lock port access and blacklist unregistered USB external drives.
Here is our list of the best USB Port Locking Tools:
- ThreatLocker Storage Control – EDITOR’S CHOICE This security package for USB access management also provides security policy implementation for backup locations and logs all data access attempts as well as controlling them. Access a free demo.
- ManageEngine Device Control Plus – FREE TRIAL Device Control Plus from ManageEngine is a comprehensive DLP software solution that enables you to track and restrict USB access throughout your network. By keeping an eye on network activity between your endpoints and USB flash drives, you can spot dangerous malware and stop it from accessing your sensitive data. Download the 30-day free trial.
- Drivelock By using both the drivelock USB restrictions and the integrated encryption and antivirus system, Drivelock establishes itself as an excellent endpoint protection solution, and completely protects your devices from USB-based malware attacks.
- Endpoint Protector Endpoint Protector by CoSoSys is a cross-platform solution that guards your network against malicious USB firmware-based attacks at each endpoint.
- Gilisoft USB Lock Because it offers a very basic set of port locking options that only work on the device that the software is installed within, Gilisoft USB Lock is primarily made for small business networks.
- Symantec DLP The complete data loss prevention (DLP) package, Symantec DLP has capabilities for locking USB ports as part of its feature-rich toolkit that also includes endpoint monitoring and comprehensive compliance reporting.
- URC Access Modes For small enterprises, especially those worried about cost, URC Access Modes is a freeware option with minimal functionality that nonetheless offers sufficient protection to meet your USB port locking needs.
Infected USB Risks
Between 2010 and 2015, the practice of disseminating deliberately infected USB drives in public arose as an odd but unexpectedly efficient method of spreading malicious software. Curious people would pick up these flash drives, plug them in at work or school, and then spread whatever dangerous software was on the firmware throughout the network.
Although this technique is frequently used with USB flash drives, it should theoretically work with any device that connects to a USB port. As a result, be wary of any unknown peripherals, and as a network administrator, make sure to warn and instruct your users about the risks of plugging in arbitrary USB devices.
Malicious viruses merely infect a host device, such as a laptop PC, and when a USB drive is connected, it modifies the firmware of the drive to spread the same infection to any devices it connects to. It can swiftly propagate malicious firmware throughout an entire company, then to other firms and beyond by repeating the same cycle of virus-based USB firmware.
Due to increased awareness of the risks associated with plugged-in wild USB devices, this problem has decreased in frequency in recent years. However, it is still something to think about, particularly given the market's dominance by USB-centric devices.
Data Loss
USB external drives are also a major source of data loss, owing to the fact they can quickly transfer vast quantities of data with internal access. There are several ways to prevent data loss that strikes at the heart of the issue; namely better internal security, data restrictions, and other more applicable methods. However, a simple solution for many is to employ USB control software to restrict USB access and encrypt USB accessible data on your network.
USB Control Software
Device control software is one of the best solutions you can use for your network. This software keeps track of and regulates any data moving between the devices on your network and any portable storage, such as USB flash drives. Data Loss Prevention (DLP) software and device control software go hand in hand, and you'll note that several device control solutions are included in full DLP software suites.
You can use device control software to physically ban any unwanted USBs on your network by giving a single point of control for all connections from external devices. As an alternative, if you continue to let flash drive connections, you can keep track of the data sent and mark those that might be dangerous.
This article discusses 6 different USB Port Locking Tools that will allow you to completely restrict USB access on your network.
The Best USB Port Locking Tools
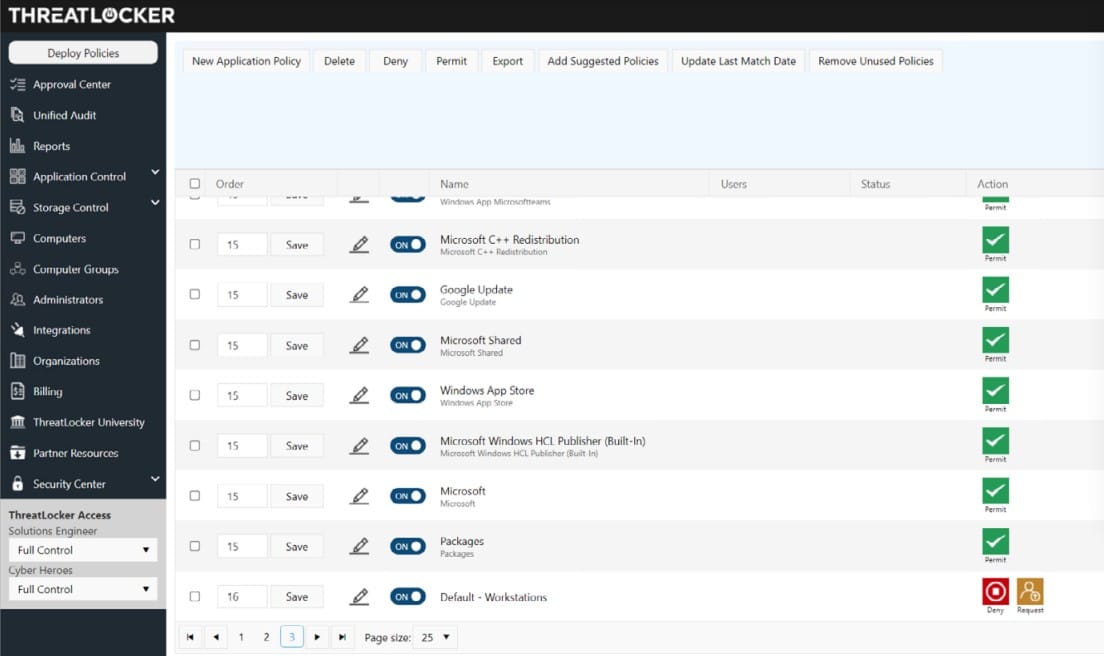
1. ThreatLocker Storage Control – GET DEMO
ThreatLocker Storage Control is part of a suite of system security tools and it provides activity logging for file movements as well as controls over the use of USB devices on a site. The Storage Control system integrates the monitoring of file movements into a system-wide data protection policy, which is formulated through a central console. By default, all USBs are blocked from attaching to any computer on the network.
Key Features:
- Default block on all USB devices
- User requests for deployment
- Centralized controls
- Location checks
- Activity logging
The central console includes controls over many aspects of system security apart from USB device control through the other modules of the ThreatLocker platform. These enable data and applications to be ringfenced, only allowing specific applications to access specific data stores and for listed users. This is an expansion of a typical access rights management system that usually only amps user permissions to resources or to software. The ThreatLocker combines user, resource, and application in a permissions combination.
ThreatLocker doesn’t publish a price list. The tool can also be deployed in combination with remote monitoring and management tools, including N-able N-sight, NinjaOne RMM, and Atera. You can get to know the ThreatLocker system by accessing a free demo.
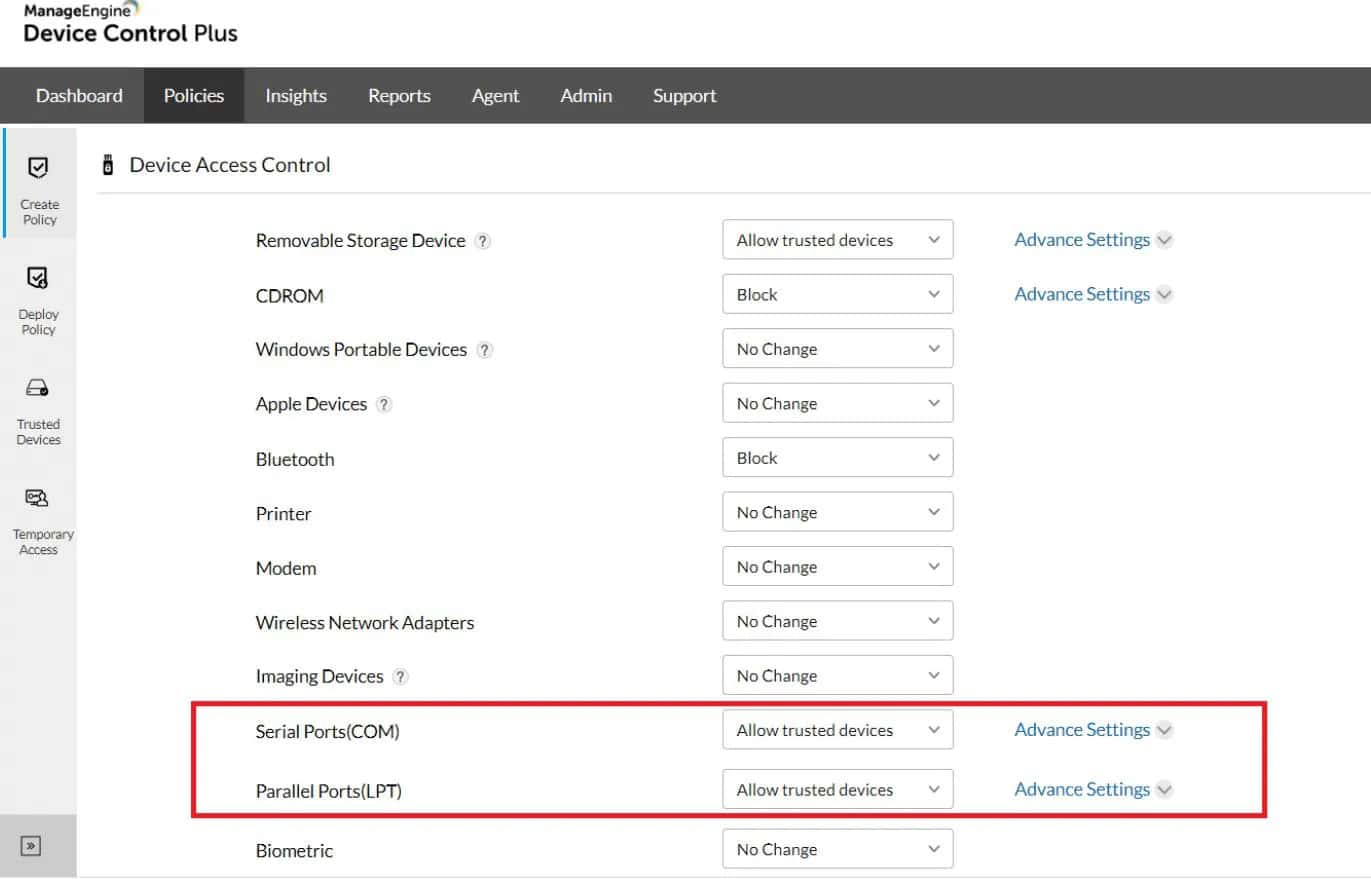
2. ManageEngine Device Control Plus – FREE TRIAL
ManageEngine Device Control Plus is a complete DLP software solution that allows you to monitor and block USB access across your network. You can detect dangerous malware and prevent them from accessing your sensitive data by monitoring network traffic between your endpoints and USB flash drives. Other features include the ability to provide temporary access to your users for configurable periods, which can prevent productivity slow-down when you need to quickly access something that is knowingly safe but isn’t fully registered.
Key Features:
- Uninterrupted device control
- Trusted device lists for granular control
- Grant temporary access upon request
- Monitoring dashboard
- Block unauthorized USB access
The product is designed with network administrators in mind, with a simple agent rollout and monitoring dashboard for your remote network administration needs. The solution has expansive dashboarding and data auditing systems to improve your reporting and monitoring capabilities.
There is a 30-day free trial of the software available on the company website. The software works on a subscription basis, with the typical cost being around $595 per 100 devices for a yearly license. You can also pay $345 for a year-long gateway server license, which may be crucially important for your required network setup.
3. Drivelock
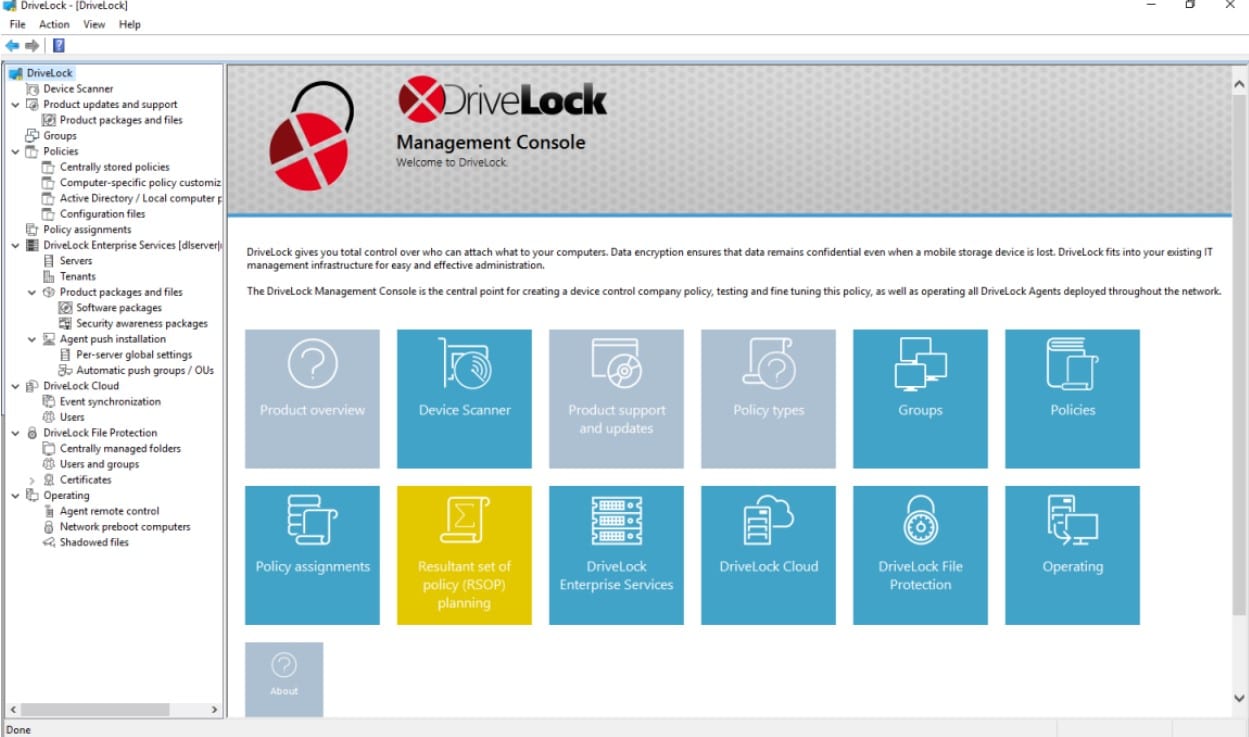
Drivelock proves itself an endpoint protection champion by totally protecting your devices from USB-based malware infection by utilizing both the drivelock USB restrictions and the built-in encryption and antivirus system. Beyond simply protecting USB flash drives, this software also enables you to decide on security limits based on each type of external storage.
Key Features:
- USB access restrictions
- Inbuilt file encryption and antivirus
- Network access reports
- Basic security monitoring
- Granular control based on file type
This solution presents a fairly simple set of deeply optimized functions, making it perfect for the job it advertises, regardless of your business scale. Encryption is relatively quick and extraordinarily secure, with no backdoors and 2FA capabilities. The Encryption 2-Go feature is another important feature to you for USB port locking, as it provides user-transparent encryption for external drives and data media.
You can test out the functioning of Drivelock's software for a full 30-day free trial. Pricing and subscription options are available to be determined after the trial period but costs around $70 per client.
4. Endpoint Protector
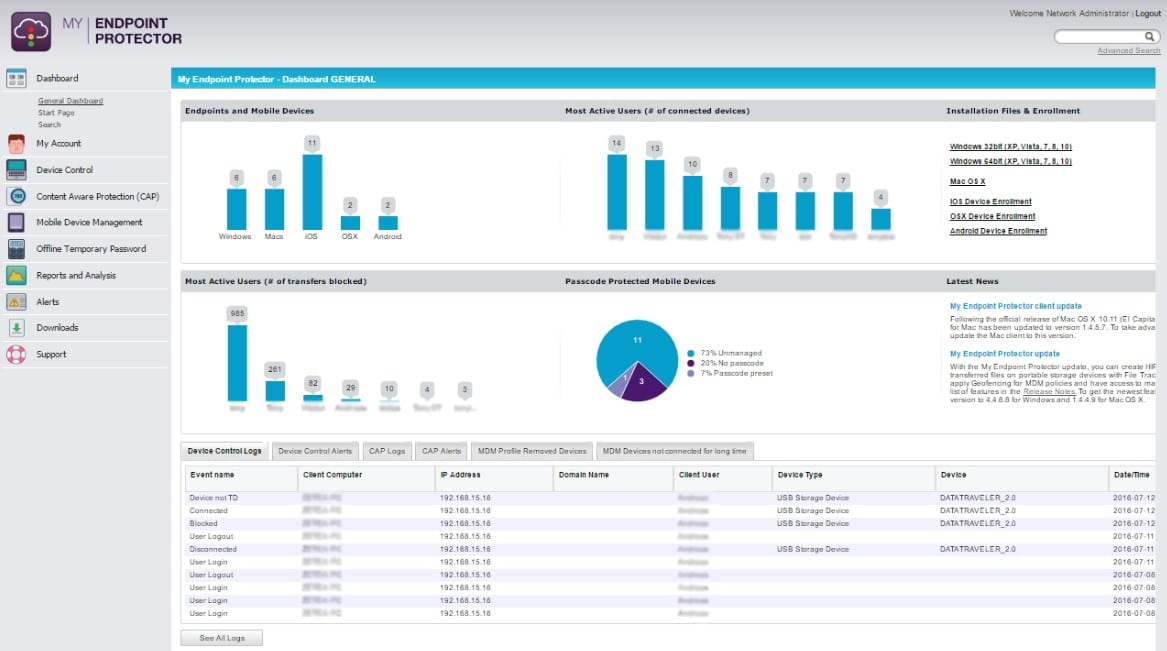
Endpoint Protector by CoSoSys has a device control feature that protects your network from malicious USB firmware-based assaults at each endpoint. The solution is completely cross-platform and requires the distribution of a single lightweight agent throughout your network. Monitoring and configuration are managed through a web-based interface.
Key Features:
- Uniquely identify connected USB devices
- Granular control over USB ports
- Reporting for USB activity
- Remote data encryption control
- Block unauthorized USB access
Along with securing USB-propagated malware, Endpoint Protector also protects your network from data leakage by utilizing data loss prevention solutions. You can additionally grant remote USB access for temporary connections, even when the device is offline. You can define policies by user, computer, or group for more granular control.
There is a 30-day free trial of the solution available from the company website. For the full price of the software, you’ll need to request a personalized quote from CoSoSys—but please note that the software has been reported to be very pricey depending on your exact requirements.
5. Gilisoft USB Lock
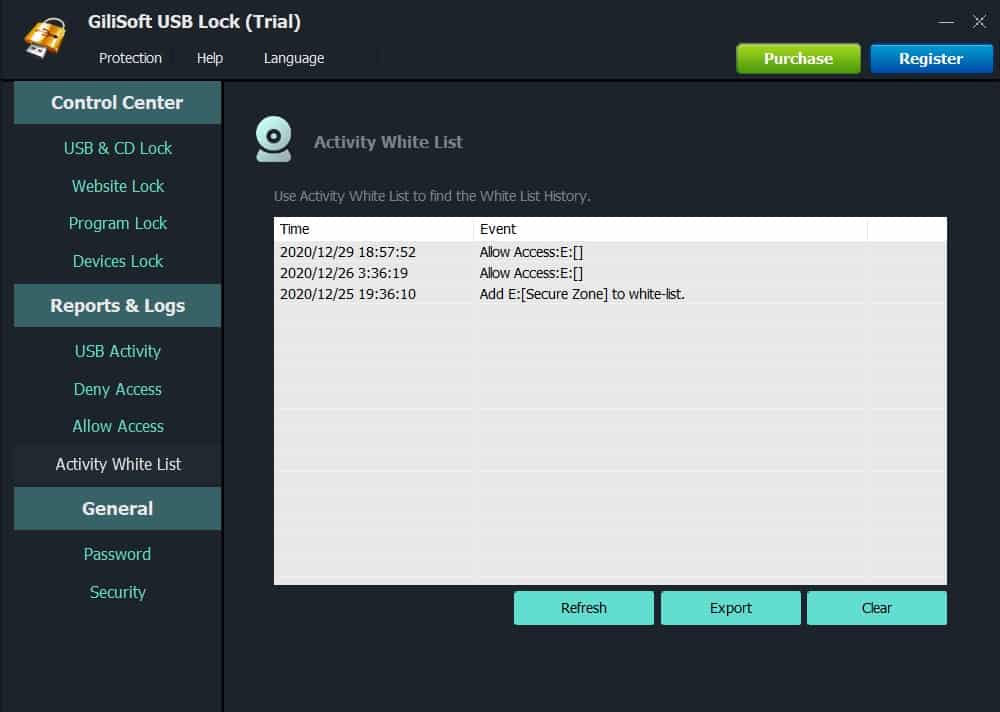
Gilisoft USB Lock is primarily designed for small business networks as it provides a very simple set of port locking tools that function solely on the device under which the software is installed. It has no centralized control features, providing only personal protection, but can be distributed across a network via a command line with pre-established settings. You can block complete access for unauthorized USB devices, and create reporting logs for compliance purposes.
Key Features:
- Block USB/SD Drives
- Trusted Devices white list
- Website and program lock
- Reports & Logs
- Powerful self-protection mode
This solution, while barebones compared to several other options on this list, is both cheap and straightforward, making it one of the best options available when you only need to secure a handful of devices.
A full trial of the software can be acquired from the website, which is perfect for feature testing, especially since the software is designed for smaller networks. The full product costs around $50 for a lifetime license on a single machine, making it suitably cheap for small business purposes.
6. Symantec DLP
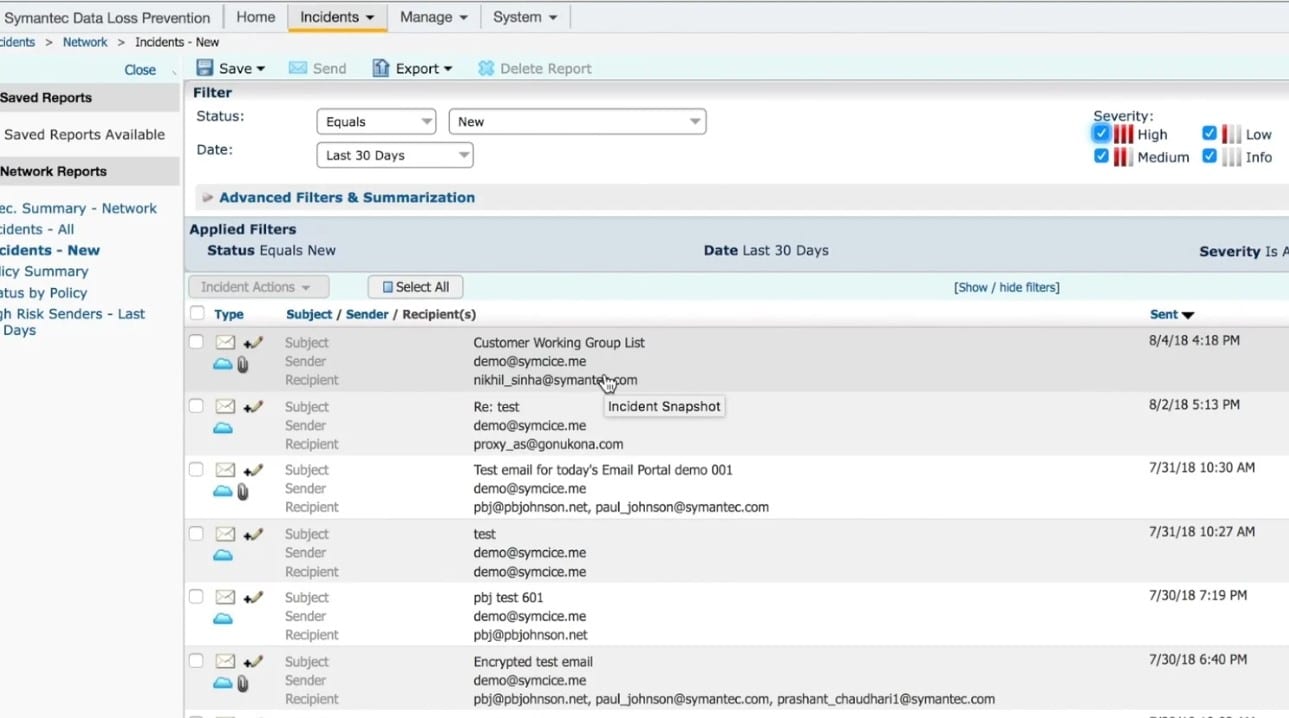
Symantec DLP is a full data loss prevention (DLP) suite that contains USB port locking tools as part of its feature-rich toolset. This solution is most suitable for large-scale and enterprise-scale businesses that need a more comprehensive DLP solution, of which one part of that solution is USB port locking.
Key Features:
- Feature-rich DLP toolset
- Critical data protection tools
- Endpoint access restrictions and reporting
- Unified policy framework
- Compliance regulations
To provide comprehensive visibility and control over your information, DLP analyzes endpoints, network file shares, databases, and other data repositories for sensitive information. The use of content-aware detection methods by DLP enables you to identify confidential information stored practically everywhere and in any file format, limit the impact of your DLP efforts on end-users, and eliminate false positives. The solution presents comprehensive compliance reporting and data encryption options.
The solution can be purchased from several Symantec partners and costs around $96 at MSRP for a full-year license of the enterprise edition. As is the case with most Broadcom Symantec products, there is, unfortunately, no trial available.
7. URC Access Modes
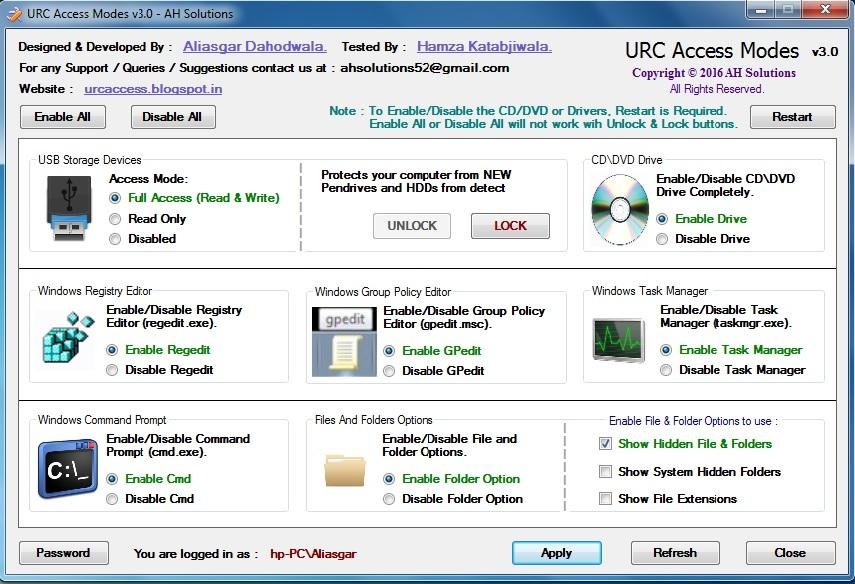
URC Access Modes is a freeware solution with barebones features but provides enough security to suit your USB port locking needs for small businesses, especially those concerned about price. The interface isn’t up to scratch compared to more premium software, but it provides port access restrictions, and several other restrictable sources such as CD drives, regedit, and command prompt.
Key Features:
- Freeware port locking solution
- Regedit restrictions
- CD drive restrictions
- Master password security
- Windows only
We would only recommend this solution for those unable to afford regular USB port locking solutions, or if port locking is a trivial issue for your business. Bear in mind the dangers presented by uncontrolled USB access, and consider stretching for more expensive solutions if you have staff who readily use USB media.
URC Access Modes is completely free to download and contains no premium features or optional extras for purchase. The solution is Windows only and is available from several freeware websites in addition to the one linked above.