Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
The Best SIEM Tools

UPDATED: June 28, 2023
SIEM stands for Security Information and Event Management. It is a blend of technologies that uses live data and log records to identify malicious activity. The purpose of SIEM is to provide a second line of defense against intrusion and insider threats. This technology is not intended to replace firewalls but it aims to catch activity that firewalls miss.
The SIEM philosophy combines two pre-existing security strategies. SIM and SEM. SIM is security Information Management and it focuses on scanning log files for indicators of suspicious activity. SEM stands for Security Event Managements and it works on live data, particularly network activity. SEM also encompasses incident response to shut down the access paths used by malicious actors.
Here is our list of the best SIEM tools:
- SolarWinds Security Event Manager – FREE TRIAL A highly-respected on-premises SIEM package that offers excellent analytical features as well as live protection. It installs on Windows Server.
- Heimdal Threat Hunting and Action Center – ACCESS DEMO This cloud service gathers data from on-premises Heimdal systems and searches for threats, sending back response instructions.
- ManageEngine Log360 – FREE TRIAL An on-premises SIEM system that collects log data from network endpoints and cloud platforms. Runs on Windows Server.
- ManageEngine EventLog Analyzer – FREE TRIAL An on-premises SIEM system that includes log file protection. Available for Windows Server and Linux.
- Logpoint – ACCESS DEMO A cloud-based SIEM that includes log management, SOAR for orchestration, and UEBA for anomaly detection baselining.
- Datadog Security Monitoring A cloud-based SIEM service that includes log management services and AI-based threat assessments. This service is able to integrate with other systems to coordinate system defense.
- Exabeam A next-gen SIEM that has integrated AI processes to identify normal patterns of behavior and deviations from that standard.
- LogRhythm NextGen SIEM Platform A combination of specialist modules that compose a full next-gen SIEM service with automated responses. Available as a cloud service, as an appliance, or as software for Windows Server.
- Rapid7 InsightIDR A combination of specialist packages that build up into a NextGen SIEM with added SOAR for threat mitigation. This is a cloud-based service.
- UnderDefense SIEM A managed SIEM service that is delivered from the cloud and includes the experts to watch over the tool and make decisions over protection strategies.
The SIEM industry is diverse and offers different solutions that cater to all types of businesses. Because there are many different requirements for SIEM configurations, we haven’t recommended one single SIEM package. Instead, we have identified the best options in a number of different categories. From this list, you will be able to narrow down your choice of SIEM, filtering out the platforms that don’t suit your preferences.
The difference between SIEM and IDS
The terminology of SIEM overlaps with that of Intrusion Detection Systems (IDSs). Intrusion detection systems aim to smoke out Advanced Persistent Threats (APTs). An APT is a situation where a hacker team gains access to a system and repeatedly revisits that system, exploring its facilities, using its resources, tampering with its records, and stealing its data.
When APTs were first discovered it was revealed that in many cases, hackers had been regular users of victimized systems for years. The purpose of these intrusions is not always to steal data. The resources of a network can be monetized by hackers. Servers can be appropriated to mine cryptocurrency and network gateways can be used as VPN proxies by hackers to front for intrusion into other networks.
APT hackers are able to adjust log file records to hide evidence of their presence or their use of resources. Highly organized and well-funded hacker teams behave like managed service providers, regularly logging in to the system and assigning around-the-clock systems administrator teams to watch over network services and ensuring that activities remain hidden.
IDS systems were created to combat APTs. There are two types of IDS. One is a Host-based Intrusion Detection System (HIDS). This looks through log files and also examines metadata about the log file to detect tampering. The other type of IDS is a Network-based Intrusion Detection System (NIDS). This scans through network traffic looking for unusual activity that doesn’t fit into the regular pattern of staff actions. The SIM part of SIEM is a HIDS and the SEM part of SIEM is a NIDS.
SIEM blends the two types of IDS into one package. This is because SIM has the benefit of spotting malicious activity by identifying a series of seemingly valid and unrelated actions that, as a chain of events, indicate an intrusion. This strategy catches threats that live monitors can’t spot. However, HIDS systems can take time to work. SEM systems operate on live data, so they can implement remediation immediately. However, there are many hacker strategies that are structured to avoid detection and so SIM doesn’t spot them.
By combining HIDS and NIDS, SIEM systems offer the best of both worlds. You can hope to catch intrusion as quickly as possible by all available methods. So, a SIEM system is the same as an IDS.
There is one more term that you need to know, which is IPS. With Intrusion Prevention Systems (IPS), prevention refers to threat remediation actions, such as blocking all connections from a specific IP address in the firewall and also interacting with Active Directory or other access rights management systems to suspend a user account.
These actions are not always implemented in SIEM systems. This type of remediation activity is called SOAR – Security Orchestration, Automation, and Response. This service interacts with other services on the network in order to shut down intrusion.
The Βest SIEM Τools
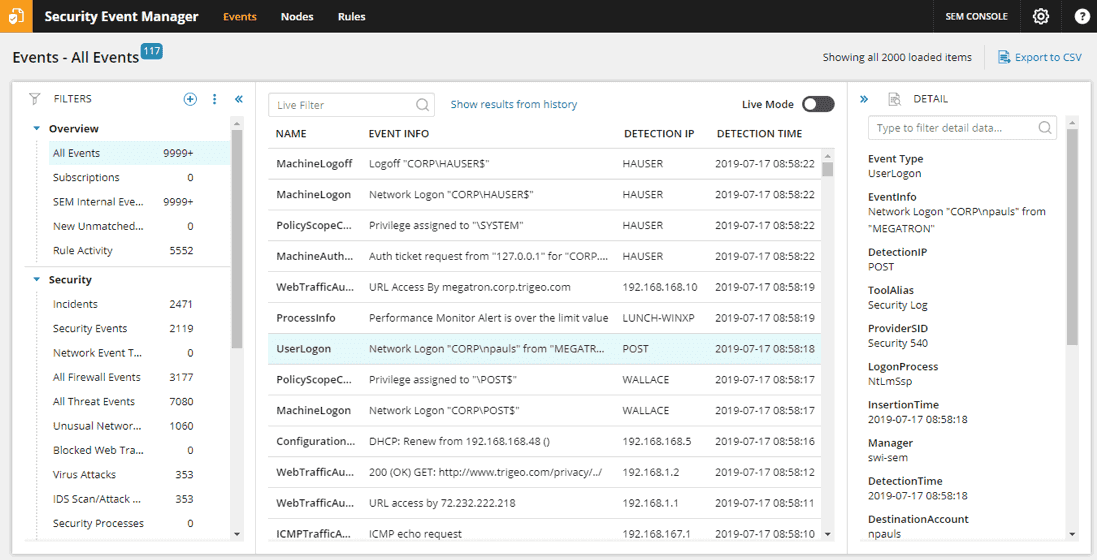
1. SolarWinds Security Event Manager – FREE TRIAL
SolarWinds Security Event Manager is a very good solution if you particularly want an onsite software package. This system installs on Windows Server.
Key features:
- Log message collection and consolidation
- Logfile management and protection
- Live network monitoring data feed spliced into log searches for anomaly detection
- Analytical tools for manual data exploration
- System alerts that identify suspicious events and can be sent out as notifications by email or SMS.
- Compliance reporting for PCI DSS, HIPAA, SOX, GLBA, and NERC SIP.
This is a very strong log file management system as well as a security operation. The Security Event Manager collects log messages and stores them in a meaningful directory structure for easy access. It then protects those directories and files from tampering. This is a vital requirement for any site-based SIEM.
The log management and security built into this system is important if you need to comply with data protection standards. The Security Event Manager will help you with compliance to HIPAA, PCI DSS, GLBA, NERC SIP, and SOX accreditation, plus other standards.
As well as logs the Security Event Manager pulls in regular reporting messages, such as SNMP reports on network device activities, so it works on live monitoring information, providing the NIDS part of SIEM as well as the HIDS functions of log analysis.
Pros:
- Enterprise-focused SIEM with a wide range of integrations
- Simple log filtering, no need to learn a custom query language
- Dozens of templates allow administrators to start using SEM with little setup or customization
- Historical analysis tool helps find anomalous behavior and outliers on the network
Cons:
-
- SEM Is an advanced SIEM product built for professionals, requires time to fully learn the platform
Price: Access the online quote engine to get a price.
Download: SolarWinds offers a 30-day free trial of the Security Event Manager.
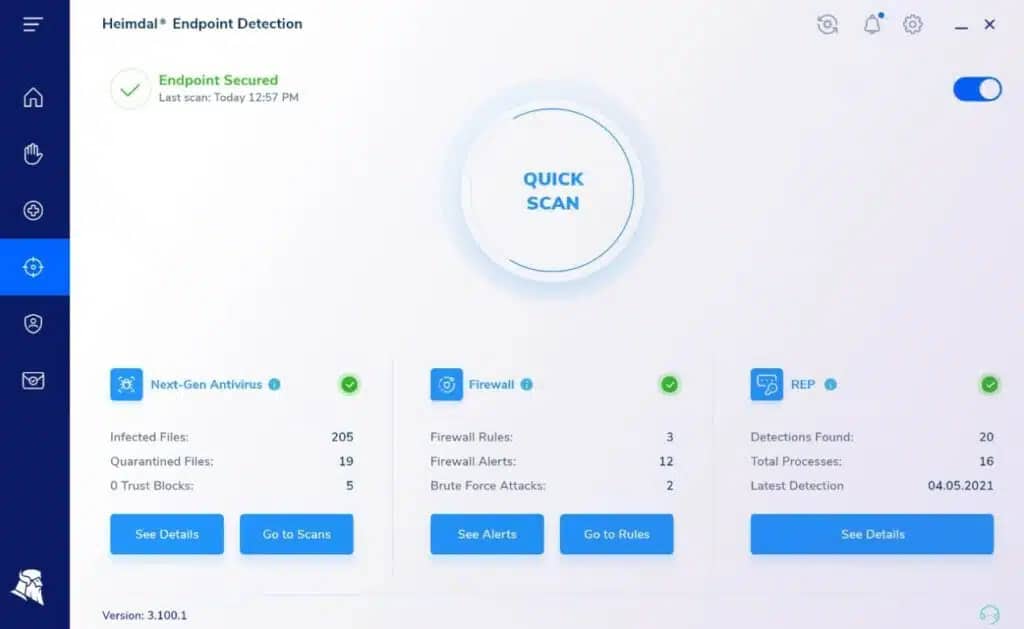
2. Heimdal Threat Hunting and Action Center – ACCESS FREE DEMO
Heimdal Threat Hunting and Action Center is a cloud-based SIEM package that receives activity reports from on-premises Heimdal tools, searches that consolidated data for threats, and sends back response instructions. This tool also performs vulnerability scanning.
Key features:
- Coordinates the activities of at least three on-premises Heimdal cybersecurity systems
- Searches uploaded activity data for insider threats and intrusion
- Performs vulnerability scanning and advises for system hardening
- Sends response instructions to on-premises systems
- Warns other devices on a network of a detected threat
- The dashboard provides overviews of system activity
The Threat Hunting and Action Center will only activate if the site has at least three different Heimdal products installed. One of these three must be the Next-Generation Anti-Virus system, which includes a mobile device management (MDM) system and runs on Windows, macOS, Linux, Android, and iOS. The other two services can be selected from Network Security, Email Security, Patching & Asset Management, and Endpoint Security.
Pros:
- Creates a private corporate threat intelligence platform
- Blocks lateral movements by malware and intruders
- Implements data loss prevention
- A flexible package with on-premises elements as well as the cloud platform
- Options to implement user activity tracking
Cons:
- Not a standalone product
Price: Heimdal doesn’t publish a price list.
Download: There is no free trial of the Threat Hunting & Action Center but you can request a demo.
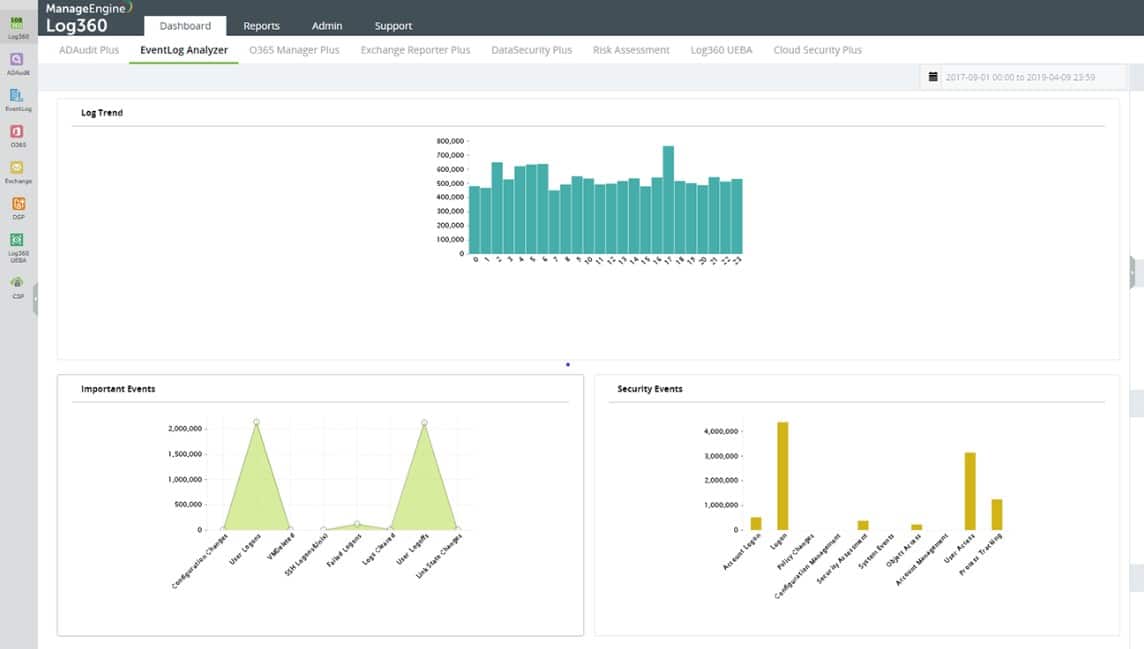
3. ManageEngine Log360 – FREE TRIAL
ManageEngine Log360 is a SIEM that installs on Windows Server and can gather log data from endpoints around the network from a series of endpoint agents. These are available for a list of operating systems, not just Windows. The tool will also take in logs sent by agents installed on cloud platforms, such as AWS and Azure.
Key features:
- Threat intelligence feed
- On premises for Windows Server
- Standardizes Windows Events, Syslog, and software logs into a common format
- Data viewer with tools for manual analysis
- Log manager that stores logs in files
- Compliance reporting for HIPAA, PCI DSS, FISMA, SOX, GDPR, and GLBA
- Monitors network endpoints and cloud platforms
The SIEM is partnered by a log server that consolidates arriving logs messages into a standard format. This enables them to be stored together in files and also loaded into a data viewer. Arriving messages are displayed in the dashboard and files can also be opened and read in for analysis.
Threat hunting is performed on arriving records on a sliding window basis. The detection algorithm is enhanced by a threat intelligence feed, which provides details on the latest hacker campaigns. Notifications about suspicious activities are displayed in the dashboard and sent through service desk systems.
Pros:
- Great dashboard visualizations, ideal for NOCs and MSPs
- Can integrate multiple threat data steams into the platform
- Offers robust searching of logs for live and historical event analysis
- Provides monitoring cross-platform for Windows, Linux, and Unix systems
- Can monitor configuration changes, preventing privilege escalation
Cons:
- ManageEngine offers a suite of advanced services and features can time to explore and test out
Price: There are three editions of Log360: Free, Standard, and Professional. You need to get a quote for the Standard and Professional versions.
Download: Register for a 30-day free trial.
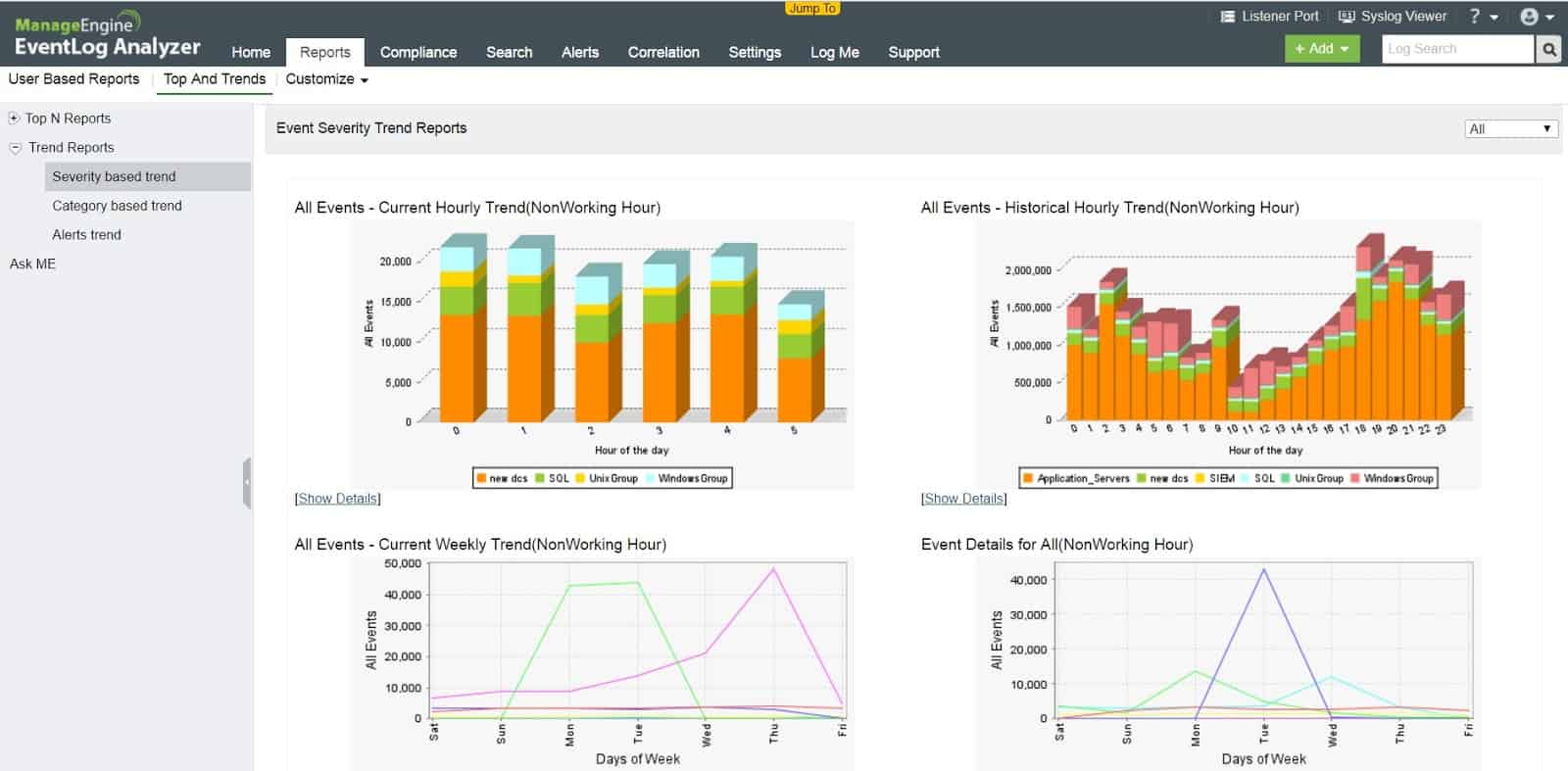
4. ManageEngine EventLog Analyzer – FREE TRIAL
ManageEngine EventLog Analyzer is a log manager and SIEM system. It offers automated intrusion detection plus utilities for manual security analysis. This is another on-premises option that can be installed on Windows Server or Linux. The EventLog Analyzer is the only option on our list for businesses that are all Linux and want to run a SIEM onsite.
Key features:
- Collects log messages, files then manages a log file directory structure and protects files against tampering.
- Includes auditing for PCI DSS, FISMA, GLBA, SOX, HIPAA, and ISO 27001 compliance
- Gathers Windows Event logs and Syslog messages plus log messages from applications and services.
- Performs live anomaly detection
- Generates alerts when a security event is detected. Those alerts can be forwarded as notifications by email or SMS.
- Supports manual security analysis.
The EventLog Analyzer collects, consolidates, and files log messages from windows Events, Syslog, and a range of application log messaging systems. It isn’t restricted to just managing the log messages generated by its host. The system also protects log files against tampering.
The EventLog Analyzer blends log file searches with live performance tracking to create both sides of the SIEM strategy.
Pros:
- Customizable dashboards that work great for network operation centers
- Multiple alert channels ensure teams are notified across SMS, email, or app integration
- Uses anomaly detection to assist technicians in their day-to-day operations
- Supports files integrity monitoring that can act as an early warning system for ransomware, data theft, and permission access issues.
- Forensic log audit features enable admins to create reports for legal cases or investigations.
Cons:
- Takes time to fully explore all features and tools on the platform
Price: EventLog Analyzer is available in three editions:
- Free – manages up to five log sources
- Premium – for a single site, the price starts at $595
- Distributed – for multi-site implementations, price starts at $2,495
Download: ManageEngine offers EventLog Analyzer on a 30-day free trial.
5. Logpoint – ACCESS FREE DEMO
Logpoint offers a converged SIEM – that term refers to a combined SIEM, UEBA, and SOAR package. UEBA refers to behavior baselining by tracking the regular activity of each user account and device. The threat-hunting service in Logpoint is an anomaly detection system that looks for deviations from the established norm.
Key features:
- Anomaly detection with AI-based baselining
- Log collection and application activity report gathering
- Log management
- Cloud storage space for log files
- Log analysis tools
- Good for compliance with GDPR, CCPA, and SCHREMS-2
- Hosted system with software maintenance included
The SOAR part of the Logpoint package is a security orchestration, automation, and response service. This uses integrations and APIs to communicate with third-party trolls. Actions taken by this system include the gathering of activity data directly from applications and automated responses that are implemented by sending instructions to other security tools.
The main package of Logpoint is hosted in the cloud. On-site actions are implemented by an agent that needs to be installed on one of your servers. This system collects data that is uploaded for threat hunting and it also communicates instructions to this-party tools in order to mitigate detected threats.
Pros:
- Automated data collection, threat hunting, and mitigation
- Monitors applications, servers, and networks
- Includes cloud platform monitoring
- Special integration with SAP for monitoring
- Alert prioritization
Cons:
- No price list
Price: The Logpoint service is priced on data throughput volumes so the process of finding out the cost of the system is interactive. You need to get a quote to find out the price for your implementation.
Download: Start by registering for a free demo.
6. Datadog Security Monitoring

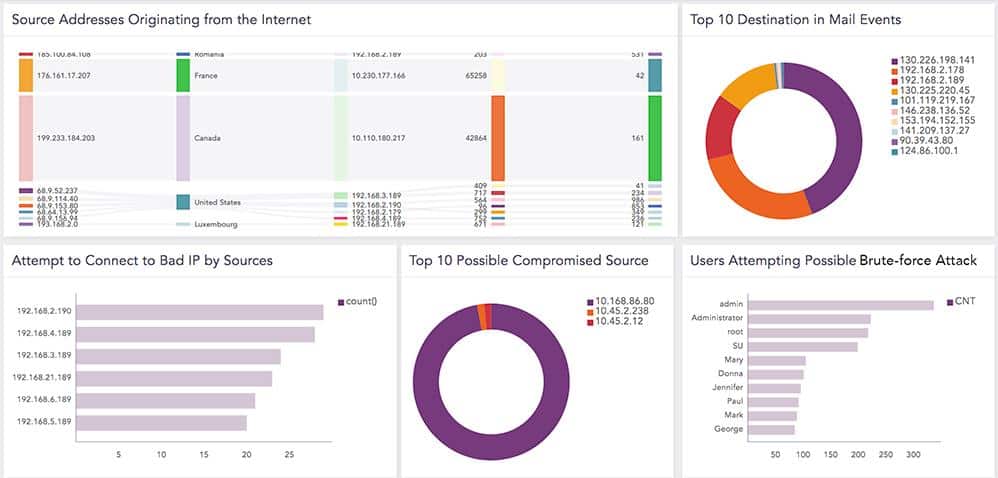
Datadog Security Monitoring is a SaaS system that can monitor networks anywhere. The service operates on log files and also collects live network traffic data, making it a SIEM system. The system looks for “signals” of malicious activity and lists all of these in the console as it detects them.
Fortunately, the Datadog service doesn’t just show those signals, it marks them within its threat hunting module and then looks out for further signs of intrusion. This means you can see evolving investigations but you don’t need to do anything about them until the Datadog system identifies a certain chain of events that amount to indications of compromise.
The overview screen in the dashboard for the Datadog Security Monitoring service shows you exactly how comprehensive this tool is, grabbing event data from all across your IT system. The service retains log messages for 15 months, which makes it a great service for standards compliance, that requires log data access for auditing. These logs are also available for security analysis.
Pros:
- Lightweight cloud-based tool
- AI powered alerts help cut down on false alarms and alert fatigue
- Live reports make it easy to see high-level metrics and drill down quickly
- 450+ integrations to fit nearly any network environment
- Scalable pricing based on how much data is processed
Cons:
- 14-day trial is a bit short
Price: Datadog Security monitoring is offered on subscription, which effectively is a pre-paid service that gets you credits for the system. The charge rate is based on the volume of data ingested per month with a rate of 20 cents per Gigabyte of analyzed logs. There is also a metered pay-as-you-go service, which is charged at a rate of 30 cents per Gigabyte of data.
Download a fully functional 14-day free trial.
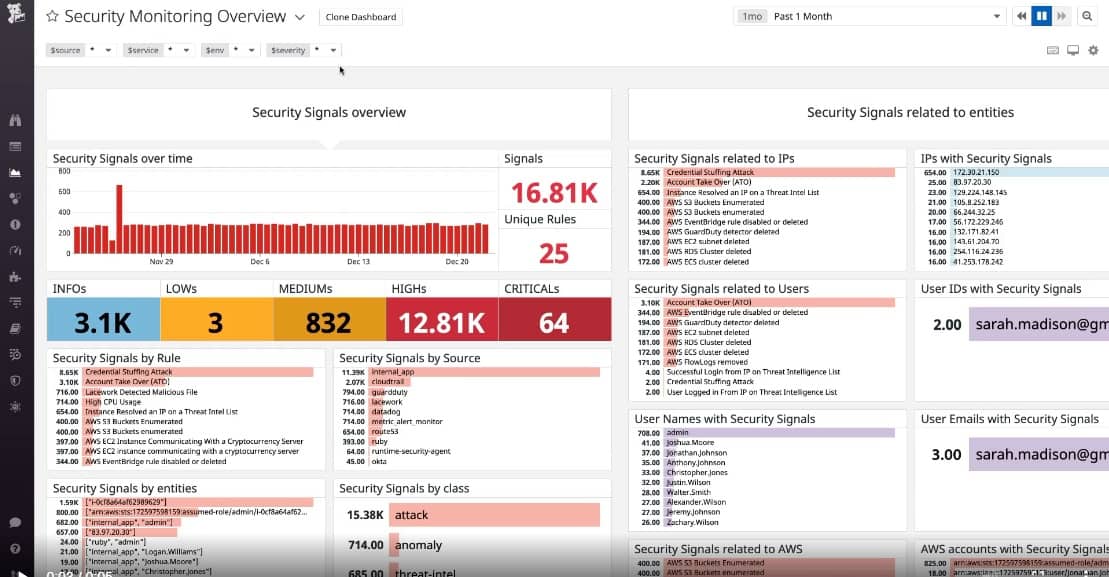
7. Exabeam
Exabeam is a NextGen SIEM service and includes threat hunting that deploys User and Entity Behavior Analytics (UEBA). This is an AI-based system that works out what is normal activity on your system and then identifies deviations from that standard, earmarking them for deeper investigation.
Key features:
- Machine learning UEBA to avoid false-positive reporting.
- SkyFormation threat intelligence feed pulled from more than 30 cloud platforms.
- High-speed threat hunting performed on Exabeam servers.
- Secure uploads for log messages from your site to the Exabeam server.
- Live detection processing shown on the dashboard identifying potential threats as they occur.
- Incident Responder – a SOAR mechanism for automated threat remediation.
- Support for manual analysis of threat data.
The Exabeam service is notable for the very high quality of its Cyber Threat Intelligence feed (CTI). This is a notification of new attacks that are emerging around the world – once hackers develop a new strategy, they implement it with a series of attacks on many businesses. The Exabeam feed gives you immediate protection as soon as a new (zero-day) attack is experienced elsewhere.
Exabeam also offers a SOAR system that will interact with other security products on your site, such as firewalls, to automatically shut down attacks.
Pros:
- Supports incidents response workflows, playbooks, and automation
- Offers usefully query features for filtering large datasets
- Can be used for compliance reporting and internal audits for HIPAA, PCI DSS, etc.
Cons:
- Lacks live network monitoring capabilities
Price: Exabeam doesn’t publish its prices. Instead, it enters into a conversation with potential customers that request a demo of the system.
Download: You don’t need to perform a download to access Exabeam. However, you can access a demo version online.
8. LogRhythm NextGen SIEM Platform

LogRhythm NextGen SIEM Platform is a well-established SIEM service that has been in production since 2003. The service is now updated to the Next-Generation SIEM category with AI-based processes and a threat intelligence feed.
Key features:
- A choice of a software package, a network appliance, or a SaaS platform.
- Log management and indexing.
- A threat intelligence feed that modifies threat hunting activities to make them focused and faster.
- Automated threat responses.
- Optional UEBA to reduce false-positive reporting and pre-filter log messages for relevant events.
- An optional live network monitor.
- Disaster recovery procedures.
LogRhythm starts off as a software package for installation on Windows Server. The current system is available for installation. However, the SIEM is also offered as an appliance and as a SaaS system.
The LogRhythm system is a bundle of specialized modules, called the XDR Stack. The layers in the stack are:
- AnalytiX, a log scanning threat hunter
- DetectX, which is the application of threat intelligence
- RespondX, which provides threat remediation by SOAR
The LogRhythm system also has two add-on modules, which are User XDR, a UEBA system, and MistNet, Network Detection and Response (NDR) service that provides live threat monitoring.
Pros:
- Uses simple wizards to setup log collection and other security tasks, making it a more beginner-friendly tool
- Sleek interface, highly customizable, and visually appealing
- Leverages artificial intelligence and machine learning for behavior analysis
- Does an excellent job at live data processing
Cons:
- Would like to see a trial option
- Data correlation could use improvement
Price: You can contact the Sales Department of LogRhythm to get a quote.
Download: There is no free trial download. However, you can access a demo version of the SaaS platform.
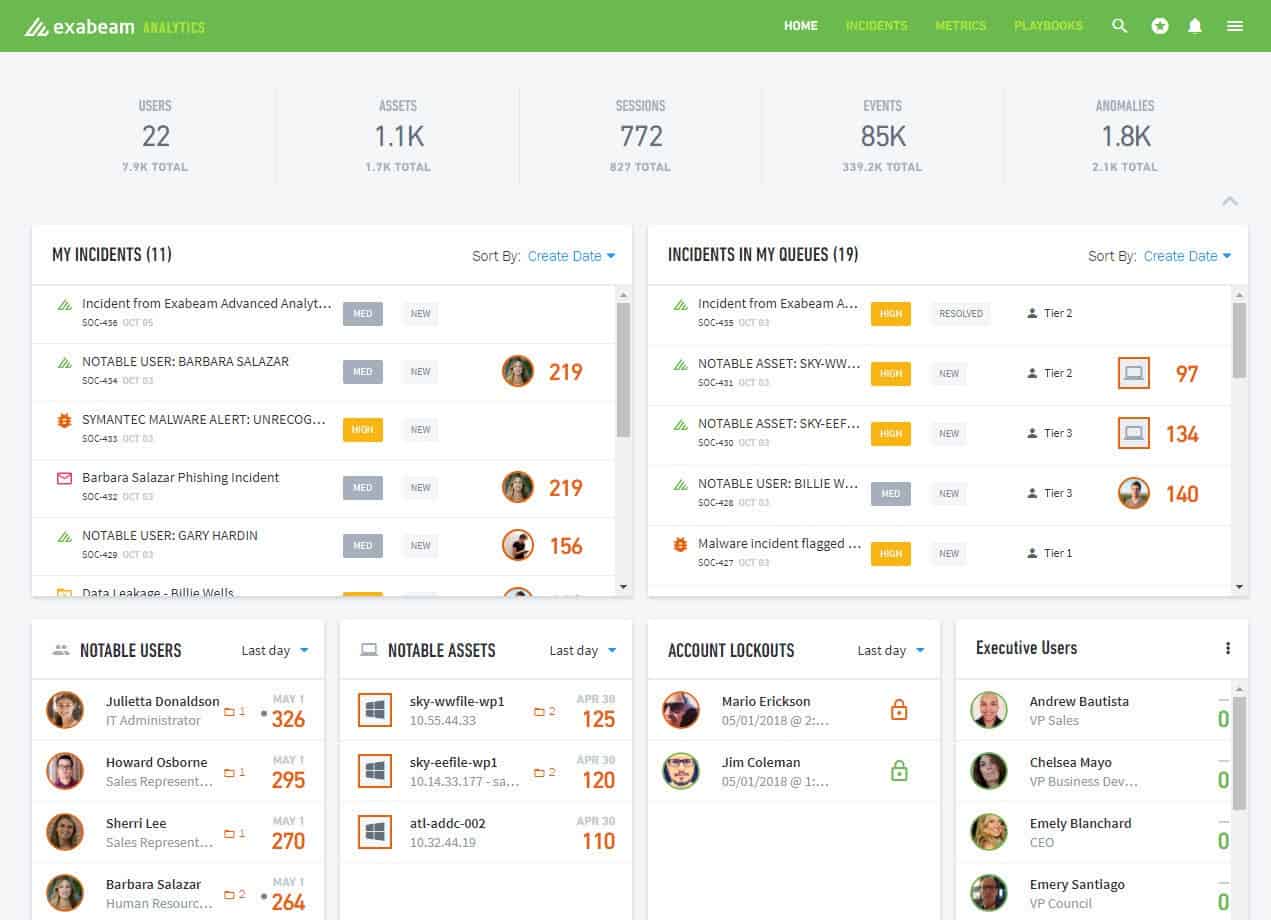
9. Rapid7 InsightIDR
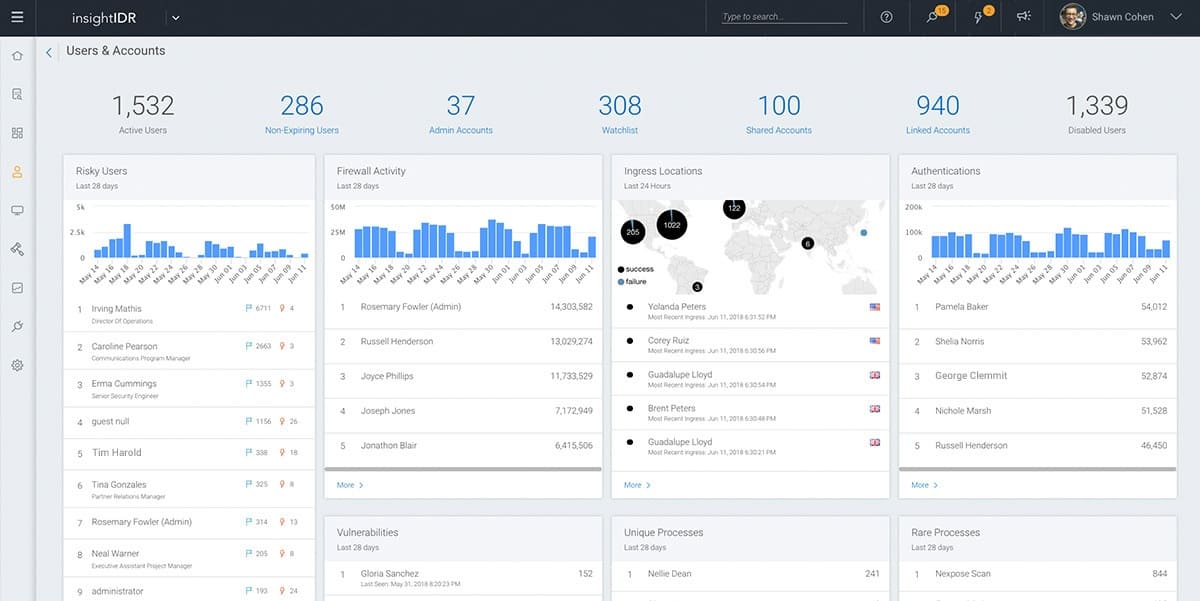
Rapid7 InsightIDR is a cloud-based SIEM that also includes network monitoring and Endpoint Detection and Response (EDR). This service is advertised as an XDR, which stands for Extended Detection and Response, however, it is still a SIEM – and a NextGen SIEM at that.
Key features:
- An on-site log collector and a cloud-based log consolidator.
- Communications over encrypted connections.
- Threat hunting informed by a live threat intelligence feed.
- UEBA for more accurate activity baselining.
- Processing and log file storage included.
- Deception technology to attract and divert intruders.
InsightIDR has all of the classic elements of a next-generation SIEM, notably, a UEBA system and an intelligence feed. The threat intelligence service is termed “attacker behavior analytics.” This is a database of indicators of compromise that gets constantly updated as the operating SIEM instances running for all Rapid7’s customers report into a common intelligence pool.
Rapid7 cloud service includes all of the processing power and log file storage space you need. Onsite protection is enhanced by deception technology that creates honeypots to force data thieves into the open and traps to keep intruders away from valuable data.
Pros:
- Leverages behavioral analytics to detect threats that bypass signature-based detection
- Uses multiple data streams to have the most up-to-date threat analysis methodologies
- Allows for robust automated remediation
Cons:
- Pricing is higher than similar tools on the market
- Some features may require paid plugins
Price: The InsightIDR package is a subscription service with a price starting at $2,157 per month.
Download: Rapid7 Insight IDR is accessed online and you can get it on a 30-day free trial.
10. UnderDefense SIEM

UnderDefense SIEM is a managed service. That is one step up from a SaaS system because it includes the services of analysts and technicians to watch over the SIEM and act on its reports. Surprisingly, the package doesn’t include the SIEM software.
Key features:
- A security management team on call around the clock
- A choice of SIEM systems
- The option to host on your servers or on the cloud
- The SOC team from UnderDefense will respond to SIEM system alerts, so you don’t have to.
UnderDefense offers you a choice of SIM software to work with. It will then install your chosen system and manage it. You can decide whether to host the software on your own server, in which case, the UnderDefense technicians will get remote access.
Pros:
- Is a co-managed service, great for businesses that don’t want to build larger cybersecurity teams
- Offers access to on-call experts
- Features a highly customizable and elegant dashboard
- Offers vulnerability prioritization
- New users get their first month free
Cons:
- Better suited for enterprises and large networks
Price: Fees start at $6 per month per endpoint plus the cost of your chosen SIEM package. Contact UnderDefense for a quote.
Download: There is no download for this service but you can request a demo.