Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
Access Rights Manager by SolarWinds – Active Directory User, File & Folder Permission Auditing Software!
UPDATED: August 10, 2022
Every company has to protect their information from data leaks and breaches. As hackers become smarter and adapt to new environments, IT specialists have to consider different software solutions to audit and guard their assets.
Part of a company’s assets is the different files and documents of the company. These documents' access and permissions must be protected, and this is granted by the IT manager. But managing lots of different access can be overwhelming if not planned properly.
This is where SolarWinds Access Rights Manager (ARM) comes into play.
It can easily Audit, Grant or Remove File and Folder Access in a bulk thus reducing the time that IT managers spend doing this task.
In this product review, we are going to analyze Access Rights Manager by SolarWinds, an IT security tool created to Audit and ultimately protect your network.
The Access Rights Management “ARM” was built based on five different areas.
- Permission Analysis ARM shows all permissions within a network and its resources.
- Documentation and Reporting Saves access rights events and actions and generates reports.
- Security Monitoring Focuses on monitoring the security of Active Directory, File Servers, and Exchange Server.
- Role and Process Optimization Improves Access Rights Management Processes
- User Provisioning Manages the creation/removal of user accounts, and rights
How does it work?
As explained before, this tool is helpful when you manage a company’s access to files and documents. It will help you grant or remove access from the users to information. The platform can be downloaded from their official SolarWinds website.
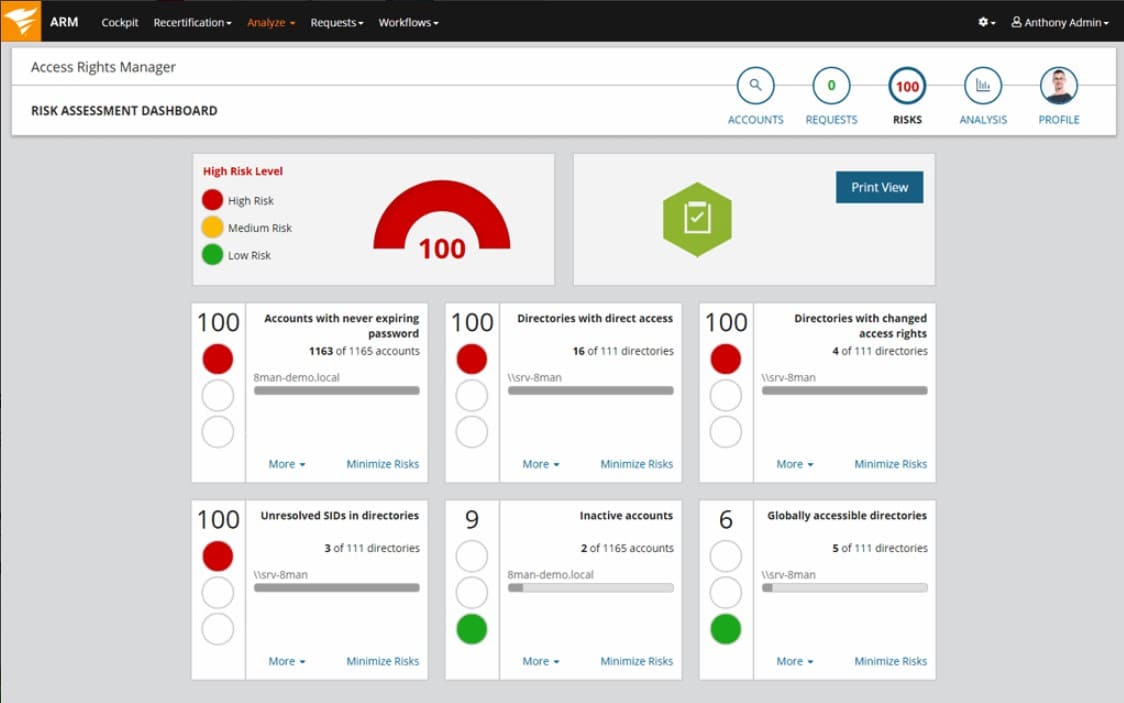
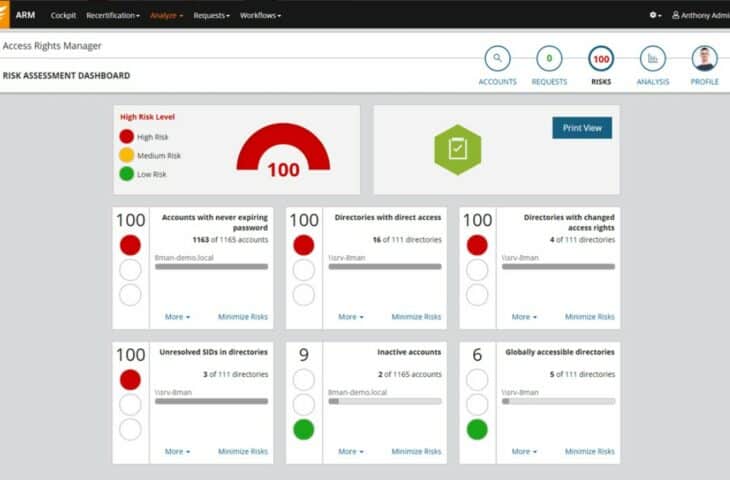
Here's how the dashboard looks like:
As you can see, the platform is very easy to use and understand. You have all the important data on the Dashboard (or Cockpit). Important information such as Inactive Accounts, Groups in Recursion, Accounts where password never expires, globally accessible directories, etc. All this information is computed into a “Risk Score”.
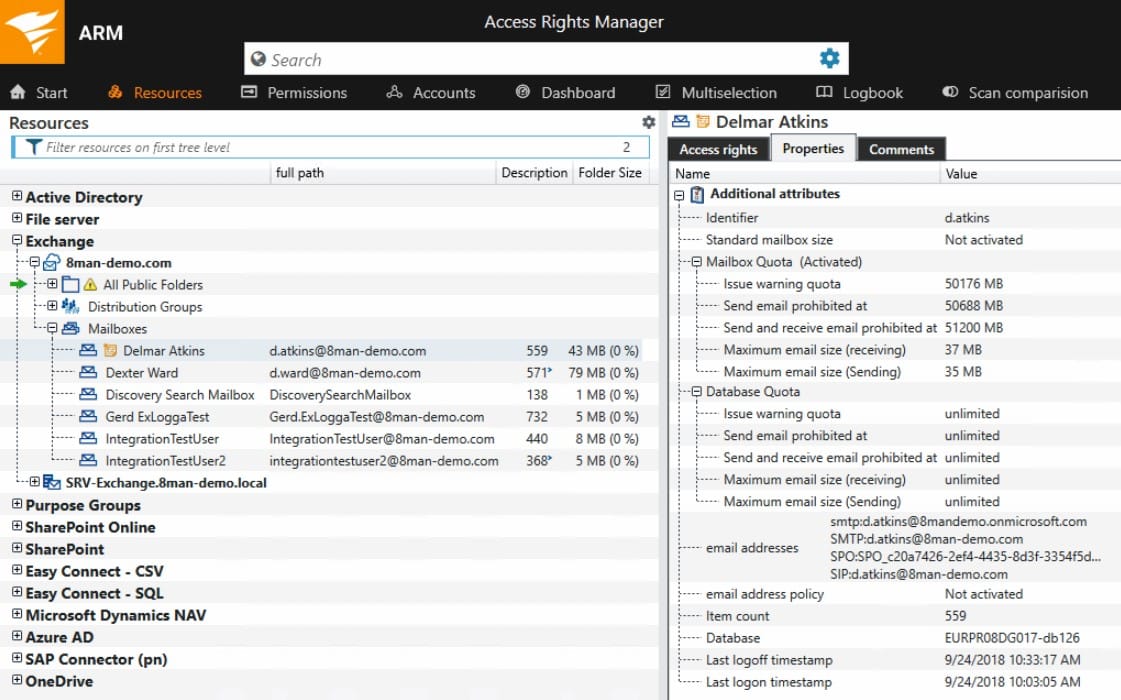
The Resources tab is where you configure the folders which include the documents you want to grant access to. Access Rights Manager can track all changes to folders, files, public folders, calendars, etc. With this, you can improve compliance and identify unauthorized events, such as file permission changes. This gives an overall insight of all the permissions on all the file servers.
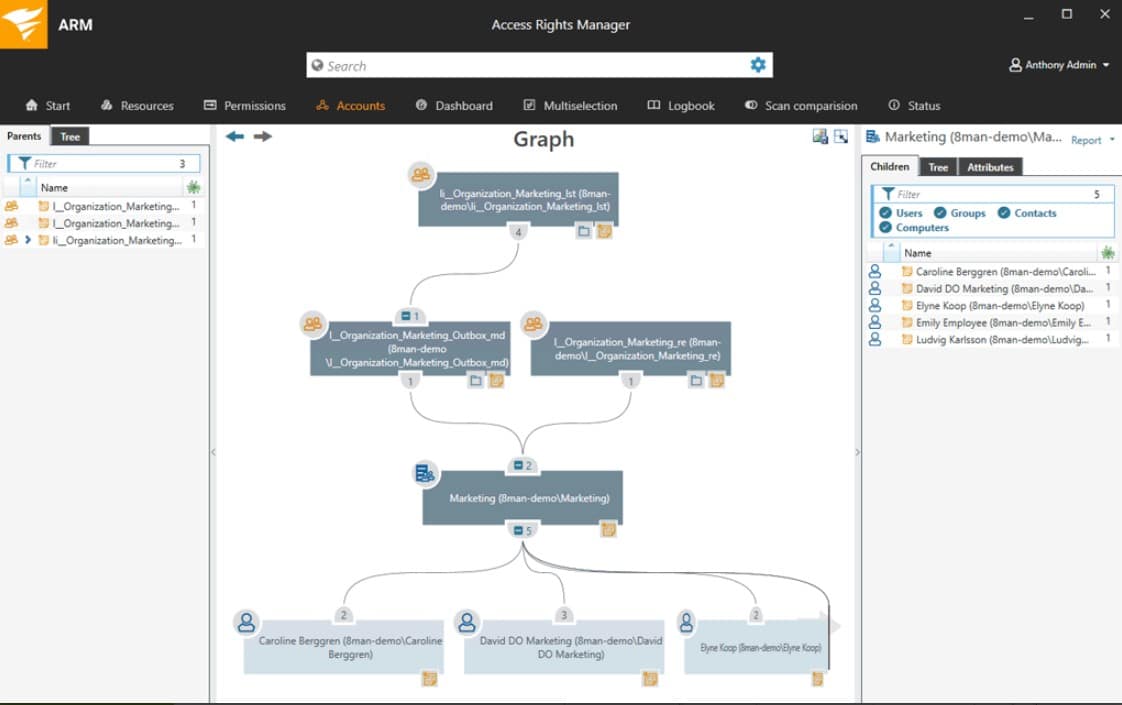
The Accounts tab is where you manage the access of the accounts. This will be in the form of a Tree, with groups working as parent and children, this is helpful when you select a parent for a permission, the children will also have the permission (unless indicated otherwise).
And this is how you add your users with the details of what groups they belong to and what resources they have access to. Once finished you can export the configuration through a PDF file and automatically send it by email.
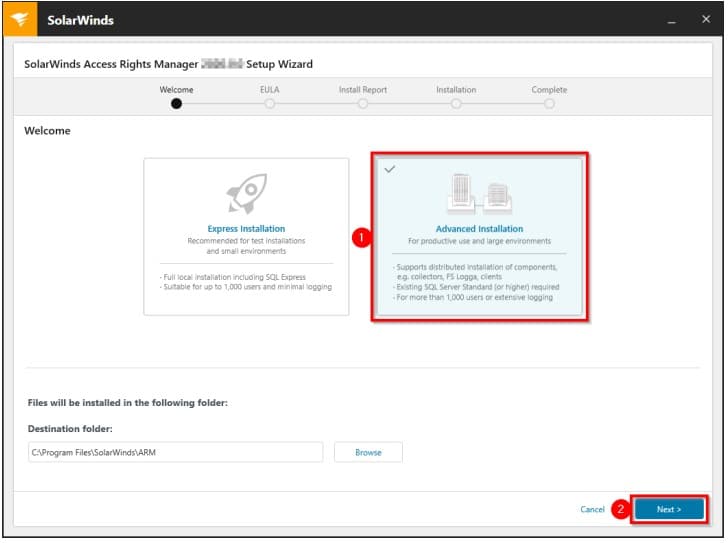
Quick and easy installation
As you download the software, you can see that it comes with Quick Install & Configuration Guide. This guide makes the installation very easy, with the step to step instructions.
When installing, select whether you are installing a Server or Collector.
Key Features
SolarWinds ARM features will improve IT security of your company by minimizing attacks coming from the company’s network itself. Access Rights Manager is popular because it allows access management and analysis processes to be automated. The list shown below contains the most important features with a brief description.
- Monitoring of Active Directory With this feature, you will be able to track the changes, and manage any sized Active Directory “AD” System. You can obtain rich data and reports, so you can analyze and audit the AD and Group Policies.
- Auditing for Windows File Share You can anticipate data outflow and prevent unauthorized changes with this feature, visualizing the access panel makes it easier to detect any risk on time.
- Monitoring of Microsoft Exchange Track any changes to Mailboxes, Email folders, and other Microsoft Exchange features, helping you to have a better control over how the information is managed.
- User Provisioning and Management You can at any time, Restrict Access to Files to Users. You can also easily Delete, Add or Modify the Users' Group membership. Provisioning and de-provisioning can be automated to save time. The tool also comes with templates that allow easy creation and removal of users.
- User Permissions Analysis This feature helps you to avoid internal security risks by monitoring user access to file servers detecting which groups the user belongs to.
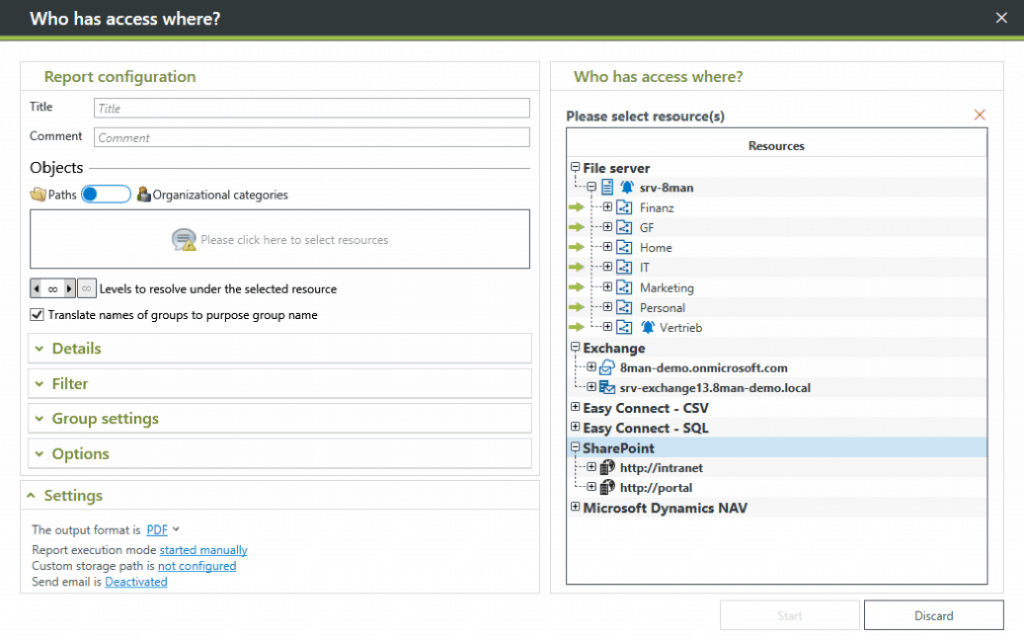
- Custom Report GenerationYou may generate reports of user access rights and activities to Audit compliance, respecting the demanded regulations of your company’s audit.
- Self-service permissions portal Request Permissions directly from data owner without going through the IT manager or the platform manager.
- Detection of Inactive and suspicious accounts Access Rights Manager can assist you in finding suspicious accounts through the use of audit trails.
System Requirements
The main server requirements are categorized in a range depending how many users you are setting (from less than 1000 to 4000 or more), and it varies from 30 to 40 GB of Hard Drive and from 4 to 16 GB of memory.
- This software will operate with a Dual core processor or better.
- It works with Microsoft Windows Server 2008 SP1, 2008 R2, 2012, 2012 R2 and 2016 as the operating system.
- The supported databases are SQL Server 2008 SP1, 2012, 2014 and 2016.
- Access Rights Manager requires .NET. 3.5 and .NET 4.5.2 (and above versions).
Price: Download and test the software on your network with a 30-day free trial. You'll be surprised that the flexibility it has overall!
Download from SolarWinds.com: https://www.solarwinds.com/access-rights-manager
The price will vary depending on the number of users you will configure (this is how it is licensed), but it starts from $2,995 thereafter.
Download the 30-day FREE TRIAL
Conclusion
The Access Rights Manager by SolarWinds will help you mitigate the risk of potential threats, allowing you to manage your users in a user-friendly platform. You will also be able to add and remove users integrating them in different groups, depending on their permission level.
This tool will help you to respect the compliance requirements of your company by generating compliance reports. All of this by increasing productivity, since you IT manager won’t lose more time in finding the threats, as the tool makes it very visible.