Our funding comes from our readers, and we may earn a commission if you make a purchase through the links on our website.
Forcepoint DLP Review & Alternatives
UPDATED: November 7, 2023
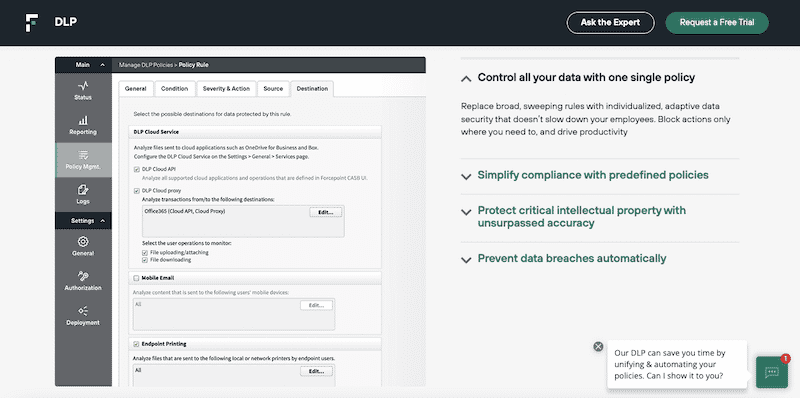
The Forcepoint DLP is one of the leading data security solutions to prevent data loss or theft. It provides the right degree of visibility and control for sys admins of anywhere employees work or data lives. One of the highlights of Forcepoint DLP is that it offers innovative features for detecting data leaks, such as OCR and Drip DLP. Still, if you are looking for a DLP solution that is easier to deploy and use, or perhaps a DLP dedicated only to endpoints or devices, you might have to look elsewhere.
In the first section of this post, we provide a Forcepoint Data Loss Prevention (DLP) review along with the pros and cons. In the second section, we provide seven of its best alternatives.
Forcepoint Review
Forcepoint DLP (Data Loss Prevention) is a world-class data protection solution designed to prevent data leakage from intentional abuse or unintended misuse. Forcepoint has been recognized by Gartner, Frost, and Sullivan as an industry leader for DLP solutions. Their DLP solution has been labeled as “leader” nine times by the Gartner Magic Quadrant.
Forcepoint DLP can stop threats wherever they arise, either inside or outside the network and protect data wherever it resides. To achieve this, Forcepoint DLP uses various features, including detection, enforced encryption, educational messages, preventive measurements, and even AI/ML.
Forcepoint DLP Highlights
Forcepoint DLP helps system admins to detect and prevent all sorts of data breaches. The solution has various features that make it stand apart as a leader.
- Help with regulatory compliance Meet and maintain compliance with +1500 pre-defined templates, policies, and classifiers.
- Central management and control Apply policies across different channels and maintain central control.
- Teach employees to protect data Instruct employees and guide their actions using instructional messages.
- Use policy-based auto-encryption to protect data as it travels outside the network.
- Identify data at rest, in motion, and in use Use methods like Optical Character Recognition (OCR), PII data identification, custom encryption identification, and drip DLP detection.
- Automatically prevent data sharing Stop sensitive data from being shared with external users or unauthorized internal users.
- Train the system with Machine Learning (ML) Find relevant, sensitive, and even unconventional data with Forcepoint's ML engine.
- Fingerprint structured and unstructured data Identify different types of data and track them down the network with fingerprinting.
- Integrated data analytics Use data analytics to identify changes in the behavior of how employees interact with data.
- Multiple channels Deploy the Forcepoint DLP solution to different and multiple channels, from the cloud to the data center.
How does Forcepoint DLP work?
Forcepoint DLP scans and discovers data wherever it lives. It can find data in transit or at-store through multiple channels such as email, web, cloud apps, endpoints, or networks. Once Forcepoint DLP finds such data, it can control it via policies or provide visibility through a centralized console.
Forcepoint DLP uses its engine and various methods such as OCR, PII recognition, custom encryption id, and drip DLP to identify sensitive data leaks. It then uses automatic mechanisms to stop the data from leaking, including messages, encryption enforcement, etc.
Forcepoint DLP Pros and Cons
Forcepoint DLP is one of the leaders in DLP solutions. Not only does it get awards from high-profile review sites like Gartner, but its users seem to embrace it quite well. Other review sites like TurstRadius also give it a high score (9.0 out of 10), while GetApp gives it a 4.7 out of 5 stars.
Below is a list of a few well-known Forcepoint SWG pros and cons.
Pros:
- It streamlines the work of admins by providing pre-defined templates, policies, and classifiers.
- Optical Character Recognition (OCR) to detect sensitive data in an image file.
- A fantastic tool for achieving and improving compliance and mitigating compliance risks.
- Unique and optimal low and slow data theft protection with Drip DLP.
- Excellent risk-based policy enforcement and behavioral data analytics.
- A fantastic tool to identify PII data and its violations.
Cons:
- The initial deployment can be difficult and time-consuming, especially with multiple servers.
- Forcepoint could improve the UI, its navigation, and User Experience.
- Forcepoint's 24/7 technical team could enhance the support.
- The knowledge base and supporting documentation could be expanded.
- Whitelisting is limited and restricted. Without this flexibility, using multi-tiered rules can be difficult.
How to start with Forcepoint DLP?
Forcepoint DLP does offer a free 30-day trial. You’ll need to register and request it from the website. In addition, you can also see the product in action if you schedule a demo.
Unfortunately, the company does not disclose the price or its available licenses if you want to compare DLP solutions based on price. You’ll have to contact a Forcepoint sales representative to get the price and request a quote based on your specific requirements.
The Forcepoint DLP Alternatives
- ManageEngine Endpoint DLP Plus – FREE TRIAL Discovers, manages, and controls access to sensitive data, including USB device controls. Runs on Windows Server. Start a 30-day free trial.
- CrowdStrike Endpoint Protection A solution that integrates Device Control (for endpoint DLP), threat intelligence, next-gen AV, endpoint detection, and response.
- Digital Guardian DLP A SaaS-based DLP solution designed for the enterprise. It is powered by AWS for faster deployment and on-demand scalability.
- Symantec DLP by Broadcom A solution designed to provide the highest data protection level while mitigating compliance risks.
- McAfee Total Protection for DLP (now Trellix) A leading DLP solution that is quite effective at protecting data from leaking across multiple channels.
- Check Point’s Quantum DLP A solution that allows admins to monitor data in-store, at-transit, and in-use. It detects and stops abnormal behaviors, all while remaining compliant.
- GTB Technologies (DLP) A unique and patented solution for enterprise-level DLP. It can automatically identify and stop data leakage across multiple channels.
- Endpoint Protector by CoSoSys A device control software leader that provides a fantastic DLP solution for endpoints.
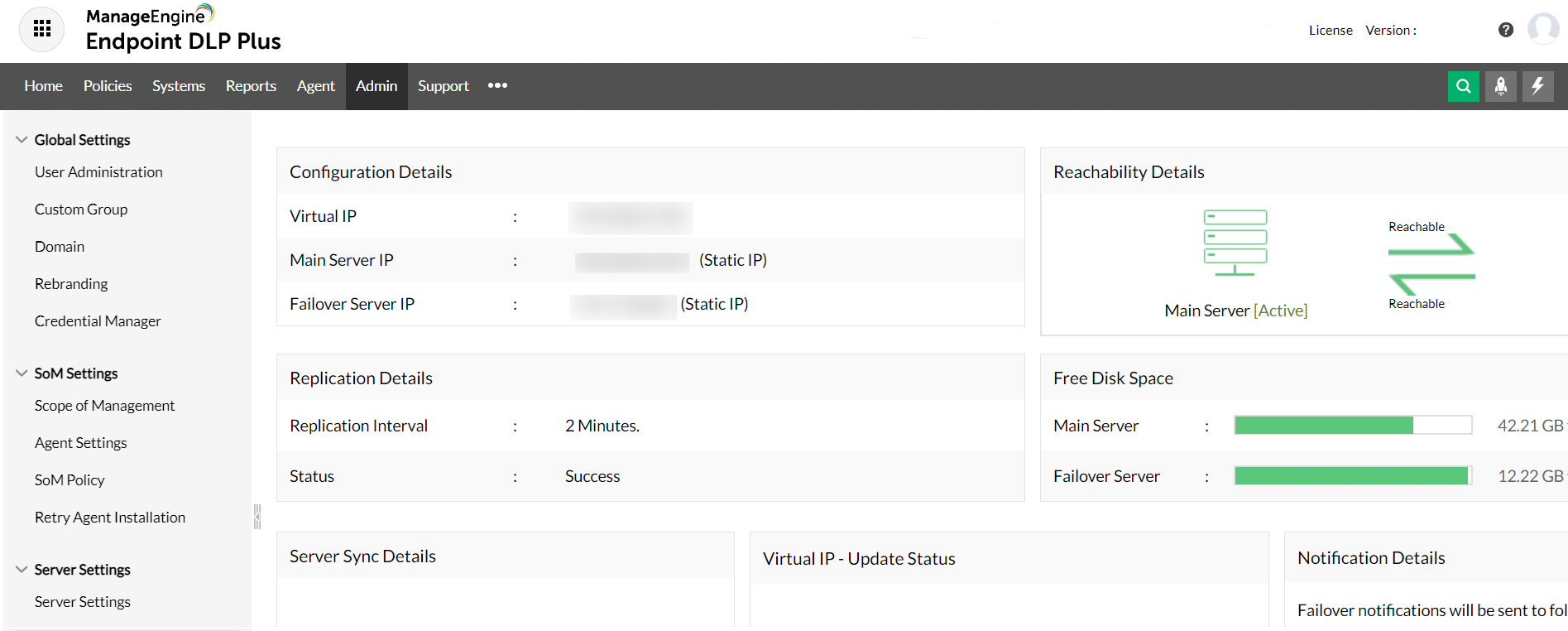
1. ManageEngine Endpoint DLP Plus – FREE TRIAL
ManageEngine Endpoint DLP Plus focuses on protecting data on a site. The tool looks at the places where data is held, which means the servers and workstations in your offices. The key function in this package is its data discovery and classification system. That process is tailored to specific data protection standards, such as PCI DSS or HIPAA. Access to data can be linked to permissions registered in Active Directory.
Key Features:
- Sensitive data discovery
- USB device control
- Data movement control
- Insider threat detection
- Account takeover protection
This system monitors all data movement channels, which includes email, cloud uploads, syncing, printing, screenshots, and USB devices. The controls on USB storage are extensive and start off with a total block on all devices. The administrator then approves specific devices by serial number. Use of those devices can be limited to specific users and the system will automatically block software on the device from activating or transferring.
Pros:
- Manage data on 25 endpoints for free
- Option for multi-site coverage
- Data containerization that restricts access
- Alerts for suspicious activity
- Automated remediation
Cons:
- Only available for Windows Server
How to start with ManageEngine Endpoint DLP Plus
ManageEngine DLP Endpoint Plus is only available for Windows Server and it only controls events on other endpoints running Windows or Windows Server. There is a Free edition of Endpoint DLP Plus that provides all of the functions of the paid version. However, the edition is limited to managing 25 endpoints. The paid version is called the Professional edition and it is priced in bands of endpoint quantities. It can also scale up to cover WANs and you can set up a failover server to ensure service continuity. ManageEngine offers the Professional edition on a 30-day free trial.
2. CrowdStrike Endpoint Protection
CrowdStrike is a leading cybersecurity company that delivers cloud-based endpoint security, cloud security, threat intelligence, and identity protection products. The company provides the extensible and flexible Falcon Platform, which uses modules and add-ons. For instance, the Falcon Platform can be used with Falcon Device Control for endpoint DLP and extended with other data protection solutions like the next-gen AV, threat intelligence, Endpoint Detection and Response, and more.
Key Features:
- Device control add-on
- Hybrid system
- On-device antivirus
- Cloud-based SIEM
CrowdStrike’s Falcon Device Control is a fantastic alternative to Forcepoint DLP if you are looking for a robust endpoint Data Loss Prevention solution at a cost-effective plan. The solution discovers and monitors all endpoints (servers, computers, laptops, mobiles, etc.). CrowdStrike products are well known for being easy to deploy and use, all while including robust features to protect endpoints from data loss and theft.
Pros:
- Continues working when the endpoint is disconnected from the network
- Coordinates firewalls across the network
- Automated responses
- Private threat intelligence network
Cons:
- Device control is a paid extra
How to start with CrowdStrike’s Endpoint Protection?
CrowdStrike’s Falcon Endpoint Protection includes Falcon Prevent and comes in different plans. Falcon Pro starts at $8.99/endpoint/month. CrowdStrike does not offer a free trial of the Falcon Endpoint Protection Enterprise software; they do, however, offer Falcon Prevent (a powerful AV to protect endpoints) for a 15-day free trial.
3. Digital Guardian DLP
Digital Guardian is an enterprise-class DLP solution based on the SaaS model. It is powered and cloud-delivered by AWS to allow fast deployment and on-demand scalability. Digital Guardian has been recognized as a leader in DLP solutions by Gartner and Forrester.
Key Features:
- Data discovery
- User tracking
- Data movement controls
Digital Guardian is an excellent Forcepoint DLP alternative because it can also find, understand, and safeguard all your sensitive data, regardless of where it resides, on the network, endpoint, or cloud. The main difference with Forcepoint DLP is that Digital Guardian works with the SaaS model and works with two products, Endpoint DLP and Network DLP.
Pros:
- cloud-based system that can monitor multiple sites from one dashboard
- Protects PII, trade secrets, and intellectual property
- A managed service option is available
Cons:
- No on-premises version
How to start with Digital Guardian DLP?
Unfortunately, Digital Guardian does not offer a free trial, but you can register and schedule a free demo. In addition, Digital Guardian does not disclose the price for its DLP solution, so you’ll have to contact them to get a quote.
4. Symantec DLP
Symantec DLP by Broadcom is an information security tool that belongs to the Symantec Enterprise Cloud. It has been labeled “a leader” in Data Loss Prevention solutions by both Gartner and Forrester. The software is explicitly designed to mitigate compliance risks and data breaches.
Key Features:
- Data discovery and classification
- Protects data on premises and on the cloud
- Compliance reporting
Symantec DLP is a fantastic alternative to Forcepoint DLP because it safeguards your data using enterprise-class discovery, monitoring, and protection technologies. The solution keeps complete visibility and control over your sensitive data regardless of where it lives (cloud, email, web, endpoints, network, or storage). Symantec is a great alternative to help you with compliance and regulatory requirements.
Pros:
- unified approach to data security across sites and cloud storage
- Provides a range of data detection methods including OCR for PDFs
- Scanning of transmission for unauthorized transfers
Cons:
- The brand has been through instability recently
How to start with Symantec DLP?
Symantec does not offer a free trial. To get to know the product, you’ll have to contact a representative to request a demo and pricing.
5. McAfee Total Protection for DLP
McAfee Total Protection (now Trellix Total Protection) is a suite of data protection tools capable of safeguarding data from leaking via endpoints, storage, network, IM, email, cloud, printing, web, and more. Total Protection includes prevention tools like the Data Loss Prevention Endpoint (McAfee DLP Endpoint), McAfee DLP Monitor, DLP prevent, and Device Control. Like the previous tools, McAfee is also a recognized leader by Gartner in Endpoint protection and DLP solutions.
Key Features:
- Data discovery
- Controls USB devices
- Also covers cloud storage
McAfee Total Protection for DLP protects on-premises endpoints but can be integrated with McAfee’s MVISION Cloud DLP to protect data from leaking through the cloud. System admins can use their on-premise DLP policies and extend them to the cloud. In addition, McAfee DLP also integrates with MVISION ePO (e-Policy Orchestrator) to streamline policy and incident management.
Pros:
- Integrates with BitLocker on Windows and FileVault on macOS
- Suitable for hybrid systems with on-premises and cloud storage
- Integrates compliance reporting
Cons:
- The new Trelix brand combines products from different companies
How to start with McAfee DLP?
There is no free trial available, but you can request a free demo of the Trellix endpoint security. To get information on pricing, contact a Trellix sales representative.
6. Check Point’s Quantum DLP
Check Point is a leader in hardware and software cybersecurity solutions. Although they are popular for their endpoint detection and protection and network firewall solutions, Quantum’s Data Loss Prevention solution is exceptional and worth mentioning. Aside from DLP capabilities, the Quantum Network Security product combines a next-gen firewall, threat prevention, Unified management, VPNs, and more.
Key Features:
- Implement through firewalls
- User education
- Data discovery templates
Regarding DLP, the solution allows system admins to monitor data movements and detect and stop abnormal behaviors while remaining compliant with regulations and standards. Check Point Quantum DLP uses the MultiSpect data classification solution to make accurate decisions and UserCheck to remediate incidents in real-time. In addition, Check Point also uses messages to educate users on properly handling sensitive data.
Pros
- Implements multiple data discovery strategies
- Blocks apps and sites that are known for data movements
- Smart Event module filters out unimportant notifications
Cons:
- Only available as an add-on to the Check Point Quanmtum Next-Generation Firewall
How to start with Check Point Quantum DLP?
No free trial is available, but you can request a free demo of Check Point’s Next-Gen firewall to see Check Point Quantum’s DLP in action.
7. GTB Technologies (DLP)
GTB Technologies is another leader in DLP solutions. The company was labeled one of the best cybersecurity companies in 2021 and, in 2016, awarded as a visionary DLP solution by Gartner. They offer unique and patented enterprise-level Data Protection and DLP platform solutions. The GTB DLP platform can quickly and automatically identify data leakages across different channels, including endpoints, mobile, network, email, cloud, or anything at the premises.
Key Features:
- Reverse firewall
- Endpoint scanning
- Data discovery and classification
The GTB next-generation data protection solution can inspect, classify, and analyze data transmissions in real-time and accurately. The solution is an excellent alternative to Forcepoint DLP as it also introduces sophisticated DLP techniques like OCR detection, encryption traffic analysis, drip DLP, real-time fingerprinting detection, and more.
Pros:
- Watches data on premises and on the cloud
- Uses a range of data discovery methods, such as OCR
- Scans outgoing emails
Cons:
- No price list
How to start with GTB Technologies DLP?
Schedule a free demo or register to download a free ‘evaluation’ of the GTB solution to understand better how the product works.
8. Endpoint Protector by CoSoSys
CoSoSys provides security products and features for device control, eDiscovery, and data loss prevention (DLP). The Endpoint Protector is a cross-platform DLP software that safeguards sensitive data from leaking through portable storage devices, mobile endpoints, or cloud-based services.
Key Features:
- Data discovery and classification
- USB device control
- Compliance enforcement
CoSoSys Endpoint Protector’s server communicates with its clients deployed on endpoints across the network; it then discovers, inspects, and protects their data flow to avoid any breaches. CoSoSys follows the HIPAA, PCI DSS, and GDPR compliance standards to help you remain compliant with industry standards and regulations. The solution can also enforce encryption on any unencrypted traffic.
Pros:
- Cross-platform operations
- Scans endpoints running Windows, macOS, and Linux
- Operates on each endpoint
Cons:
- Not a SaaS package
How to start with Endpoint Protector by CoSoSys?
Endpoint Protector can be deployed as an on-site solution (virtual appliance), as a cloud-based service, via a standalone software package, or through SaaS. You can register to get a 30-day free trial of the CoSoSys Endpoint Protector online version or register for a free demo.